Over the past few years, organisations have been combining their operational technology (OT) and IT networks, mainly due to the widespread use of Industry 4.0 and the industrial internet of things (IIoT).
Over the past few years, organisations have been combining their operational technology (OT) and IT networks, mainly due to the widespread use of Industry 4.0 and the industrial internet of things (IIoT).
However, this convergence has led to significant difficulties such as open access, lateral movement, friction between OT and IT teams, poor visibility and management, and alert fatigue.
To overcome these challenges, organisations need to implement key solutions.
First, they should identify their assets, classify them and prioritise their value. This involves creating a comprehensive inventory of all network assets, categorising them based on importance to the organisation. By doing so, organisations can focus their security efforts on their most critical assets, ensuring that they receive the appropriate level of protection.
Another critical solution is to segment the network dynamically. This involves dividing the network into smaller, isolated segments that restrict lateral movement and limit the spread of cyberattacks. By creating even smaller segments that restrict communication between devices only to what is required for their intended function, organisations can prevent attackers from moving laterally across the network.
Analysing traffic and scanning environments for threats and vulnerabilities is essential.
By monitoring network traffic for suspicious activity such as malware infections, data exfiltration and unauthorised access, organisations can identify vulnerabilities in their network and take steps to address them before they can be exploited by attackers.
By conducting regular vulnerability scans, organisations can identify potential weaknesses and gaps in their OT and IT systems, including outdated or legacy OT systems.
Controlling identity and access management is crucial to secure converged networks.
Robust control
By implementing a robust access control mechanism that restricts access to sensitive systems and data to authorised personnel only, with a strong authentication and authorisation system that ensures users are who they claim to be, organisations can prevent unauthorised access.
Furthermore, specialist OT network access control solutions are essential to address the unique security challenges of OT/IT convergence. Traditional NAC solutions primarily designed for IT networks may not adequately cater to the specific requirements and complexities of OT environments.
Securing wired and wireless access is essential and involves implementing strong encryption and authentication mechanisms for both wired and wireless access points. Network traffic must be monitored to identify any suspicious activity or unauthorised access attempts.
Endpoint detection and response (EDR) solutions are an integral part of securing converged OT/IT networks. By continuously monitoring endpoints for suspicious activities and behaviours, EDR solutions enable real-time threat detection, incident response and forensics.
They provide detailed visibility into endpoint activities, allowing for rapid identification and mitigation of advanced threats, thereby bolstering the overall security posture and resilience of OT/IT networks.
 The CISO/CIO plays a crucial role in managing the convergence of OT/IT networks. They are responsible for implementing effective security measures, ensuring compliance with regulations, identifying and mitigating risks and promoting collaboration between IT and OT teams.
The CISO/CIO plays a crucial role in managing the convergence of OT/IT networks. They are responsible for implementing effective security measures, ensuring compliance with regulations, identifying and mitigating risks and promoting collaboration between IT and OT teams.
“As more companies work towards IT/OT alignment, the CIO and the IT organisation will be at the forefront of fostering relationships and changing the culture of the organisation,” said Kristian Steenstrup, distinguished analyst and Gartner fellow. “This will require a hybrid of traditional IT and OT skills and development of new intellectual property, while experience external to the company will be tapped into to assist with cross-topic education.”
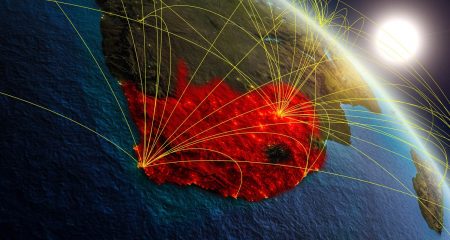
OT/IT convergence is a huge risk in South Africa, where organisations are often targeted by cybercriminals due to the perceived weakness of their security systems. This is because many companies in South Africa may not have invested sufficiently in their cybersecurity systems and infrastructure.
Secondly, the country has a lack of skilled professionals with expertise in both OT and IT systems, which makes it challenging for companies to manage the convergence effectively. Many South African companies may also have outdated or legacy OT systems, which are more vulnerable to cyberattacks.
Finally, South Africa has a unique regulatory environment, and there may be compliance issues that companies must consider when implementing cybersecurity solutions for OT/IT convergence. All of these factors make OT/IT convergence a challenge for local organisations, which need a comprehensive approach to address these issues and ensure their networks are secure and resilient.
Speak to Maxtec to see how you or your clients can safeguard critical OT infrastructure from cyber threats. Contact us for a free assessment or a demo and see how you can become a converged OT/IT security leader. Alternatively, visit www.maxtec.co.za or call 011 803 6635.
- This promoted content was paid for by the party concerned