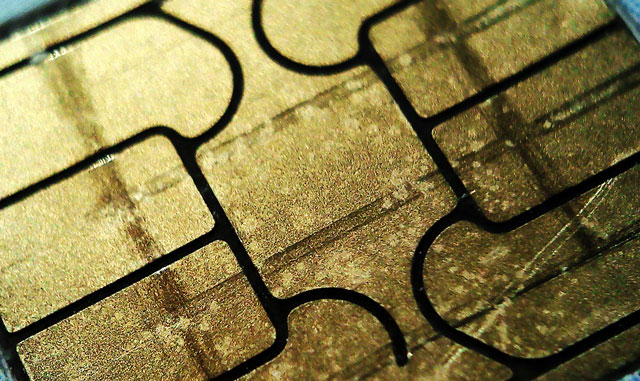
The small microchips known as “subscriber identity modules” or Sim cards that are required for mobile phones to log on to a phone network will soon be 25 years old. While mobile phones and network technology have progressed in leaps and bounds, Sim cards are still lodged in handsets.
And they’re vulnerable too — it was claimed recently that US and UK intelligence agencies stole potentially millions of Sim card security keys which would allow spies to track users and eavesdrop on calls.
Gemalto, the Dutch Sim card manufacturer that was reportedly the victim of an NSA and GCHQ attack, responded with assurances that little, if any, information was stolen. The firm stressed how important its products were to mobile phone security. But the reality is that Sim cards are now more of a drawback than a benefit.
Sim cards were a useful feature when they came onto the market in 1991. At the time, mobile phones were bulky devices, usually mounted in cars or carried on a shoulder strap. They were often rented along with a car. A Sim would help customers quickly and easily transfer their phone number and contacts from one phone to the next, without the need to type in long identifiers and access codes each time. Having to enter access codes into a phone that was essentially shared also meant users might forget to delete them before returning the device. Storing the login details in a removable personal plastic card elegantly solved this problem.
But the days of huge or rented car phones are gone, and today smartphones are lightweight, personal devices that we entrust with passwords to many sites and services — access to Wi-Fi, email, social networks, app stores and online shopping.
The fact is that the Sim could have been replaced long ago with a simpler alternative: typing in a user identifier and password directly into the phone is an option — just as we do to access Wi-Fi. QR codes — the square, 3D barcodes — are a more convenient alternative for smartphones with cameras, where an app could read the details encoded in the QR straight from the camera.
Modern cryptographic techniques mean that passwords no longer have to be very long. Password-authenticated key exchange (PAKE) techniques exist that use passwords as simple as a five-digit Pin to create highly secure encrypted connections that even the supercomputers of eavesdropping intelligence agencies cannot break. And thanks to e-mail and the Web, network operators today have much better mechanisms for keeping in touch with their users to inform them which devices are authorised. None of these options were available when the Sim was conceived in the late 1980s.
Smartphone app stores like those from Apple and Google already make good use of modern authentication techniques. They could, today, be used to easily transfer all the functionality of a Sim into the phone using an app. All that’s needed is a new standard interface for mobile operating systems such as Android or iOS that would allow apps (software) to take over the functions of the Sim (hardware). Technically, a mobile network login is no more challenging than similar applications such as payment wallets, online banking, digital rights managed content, and so on.
Vested interests
Manufacturers are understandably against anything that would eliminate their business — an estimated 5,2bn Sim cards were sold in 2014. Many network operators are also wedded to the Sim because it allows them to lock customers to their network, preventing easy access to competitors.
Modern Sims are tiny, difficult to access, and easy to lose once taken out of the phone. In fact, many users may not even know how to find or remove theirs, because it was inserted for them when they bought the phone. This inconvenience allows providers to charge high roaming fees when customers use their phone abroad, when using a local operator would be cheaper.

If the Sim were replaced with a password or extra software, users would be able to keep several pay-as-you-go subscriptions from different providers in their phone simultaneously, so they can easily switch to the most attractive rate depending on where they were. Apps that functioned as brokers could even negotiate which network to select based on best price automatically.
Another obstacle, besides the Sim itself, that hinders customers from easily switching between network providers is the cumbersome procedure required to port a telephone number. This process was designed to ease switching contracts every few years, rather than to help a phone switch between networks automatically several times a day.
But modern internet-based telephony has demonstrated that moving a telephone number between networks can be accomplished in seconds — the same needs to be implemented in mobile phone networks.
Given that the Sim card and phone-number transfer are barriers preventing customers from fully gaining the benefits of market competition, regulators should watch out that vested interests are not able to undermine efforts to provide alternatives.
The European Commission has long tried to improve mobile phone competition, mostly through price-control measures of roaming charges. Ditching the Sim would remove a major obstacle to competition, something that would likely generate market solutions to the problem of excess roaming charges without the need for further regulation from above.![]()
- Markus Kuhn is senior lecturer in computer science at the University of Cambridge
- This article was originally published on The Conversation




