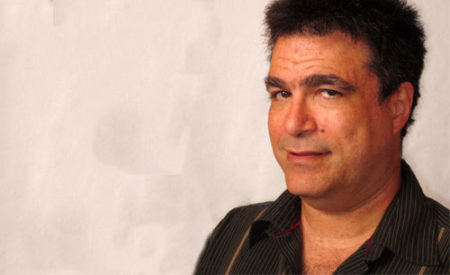
[By Nathaniel Borenstein]
Trust is traditionally the antithesis of traditional security, where experts often consider “trust no one” the best working attitude. The job of the security professional, after all, is to counter the actions of the untrustworthy. Could it possibly make sense for such people to be more trusting?
Of course not. A paranoid security professional is usually a good security professional. But that doesn’t mean that everyone else needs to share that paranoia all the time. A modicum of well-placed trust can actually make a business more secure. Wherever threats have become commoditised, businesses can outsource their paranoia, replacing it with individual prudence and trust for the outsourcer.
Consider the quotidian security guard, sitting or standing by the entrance to a building, perhaps checking identity badges or monitoring video cameras, and generally being alert to anything unusual or threatening. Nearly every business has the same needs from such a guard, and most of them outsource the task to an agency that trains, hires, and bonds each employee. Such agencies usually provide better and more cost-effective service than their customers could hope to achieve by providing the service in-house.
Computer security has long been another story. In the beginning, idiosyncratic mainframes ran idiosyncratic software with idiosyncratic security needs. Computer security inevitably grew up as an in-house function. Even by the 1990s, corporate computing environments were far from commoditised, and it made sense to bear the cost of computer security in-house.
And then came the cloud.
Cloud computing represents the convergence of several trends, including ubiquitous broadband, powerful end-user devices, and standardisation of IT services. It largely completes the transition from idiosyncratic corporate IT environments to IT as a service, and makes it possible for the first time to think about IT security as a standardised service.
With security-as-a-service, most traditional IT security functions are handled, like application services, by a cloud provider. That provider is highly specialised, and can generally be expected to operate with a level of professionalism and expertise that customers can’t hope to maintain in-house. Outsourcing security generally yields better security for less cost and effort.
The catch, of course, is the word “generally”. Inevitably, in a world of outsourced security providers, some will be better than others, and a few will screw up royally. This is why companies need to exercise real due diligence in their choice of security providers (and cloud providers in general).
It’s an important decision, but ultimately much like choosing a provider of security guards. Once you’ve made your choice, your best bet (aside from some periodic checks) is to focus your attention elsewhere. Relax, and trust your security provider to do their job, the same way you trust your other outsourced service providers and, for that matter, your employees. You can’t run a business without a high level of trust for the people on your team.
So, outsource your paranoia. Trust that the provider you’ve chosen knows what they’re doing, and — most important — do what they tell you! If they tell you to change your passwords, change your passwords. If they tell you to upgrade to two-factor authentication, do it. They can’t be effective in ensuring your security if you don’t cooperate, but you don’t need to second-guess them. You’re paying them to take the worries off your plate and tell you how to operate securely. Do what they tell you, but then relax and get on with your business.
- Nathaniel Borenstein is the chief scientist for Mimecast. Previously, he was a distinguished engineer for IBM Lotus Division
- Subscribe to our free daily newsletter
- Follow us on Twitter or on Facebook