Central Intelligence Agency hackers have developed tools letting them break into devices from iPhones and Android phones to Samsung “smart” televisions to monitor conversations and messages, according to WikiLeaks.
WikiLeaks, which specialises in disclosing government secrets, posted 8 761 documents and files Tuesday that it said came from the CIA’s Centre for Cyber Intelligence.
The trove, if legitimate, discloses malware, viruses, security vulnerabilities known as “zero days” and several hundred million lines of code used by the CIA. It also reveals that the agency has the ability to break into devices and intercept messages before they can be encrypted by applications such as Facebook’s WhatsApp, Signal, Telegram and Confide.
“At first glance it is probably legit or contains a lot of legitimate stuff, which means somebody managed to extract a lot of data from a classified CIA system and is willing to let the world know that,” Nicholas Weaver, a senior researcher at the International Computer Science Institute at the University of California at Berkeley, said in an e-mail.
CIA spokesman Jonathan Liu said in an e-mail: “We do not comment on the authenticity or content of purported intelligence documents.”
The types of hacking capabilities purportedly disclosed by WikiLeaks aren’t easily replaced once they are disclosed and targets can develop defences against them, according to a former National Security Agency cyber engineer, who asked not to be identified because of the sensitivity of the information.
The alleged leaks are a reminder of how important, yet difficult, data protection is for intelligence agencies, added the former official, who said there appears to be a crisis in operational security over maintaining confidentiality.
WikiLeaks boasted on Tuesday that its CIA leak “eclipses” the number of pages in Edward Snowden’s 2013 disclosures of National Security Agency programmes.
“It could be potentially more dangerous than Snowden,” said Bob Stasio, a fellow at the Truman National Security Project. “The Snowden leaks were damaging but were never linked to an actual threat of life that we know of. If this leak turns out to be genuine, the lives of people who have worked with the CIA could be at risk.”
Last year, WikiLeaks posted thousands of stolen e-mails to and from Democrat Hillary Clinton’s presidential campaign chairman. WikiLeaks has denied that it obtained the Clinton e-mails from Russia, which US intelligence agencies have said was responsible for hacking during last year’s campaign to hurt Clinton and, ultimately, help Donald Trump win the White House.
In an analysis it released on Tuesday, WikiLeaks said the CIA’s Remote Devices Branch has a group called Umbrage, which maintains a “substantial library” of attack methods from malware produced in other countries, including Russia.
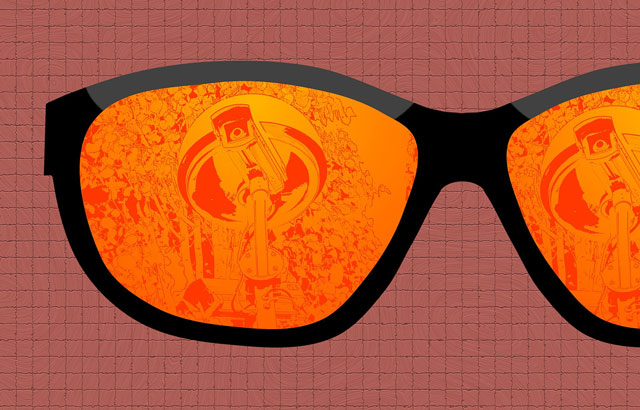
WikiLeaks said the CIA documents showed the agency is able to defeat encryption on popular applications such as WhatsApp by simply hacking into the devices “that they run on and collecting audio and message traffic before encryption is applied”, WikiLeaks said.
WhatsApp has 1,2bn monthly users, while Telegram has more than 100m. Signal was the 32nd most popular app on Google’s Play Store as of Monday, according to App Annie, which tracks app data. Telegram was 37th and WhatsApp was second.
Activists, journalists and others often turn to such outlets for secure communications, while terrorist groups such as Islamic State have used Telegram to go undetected. US intelligence and law enforcement agencies have said that they need new powers to break into encrypted applications and devices.
WikiLeaks said the material it disclosed “appears to have been circulated among former US government hackers and contractors in an unauthorised manner, one of whom has provided WikiLeaks with portions of the archive”.
While the material may reveal sensitive CIA techniques, it doesn’t list “executables or exploits” — details on actual attacks that have been carried out and the targets — according to Weaver, who was beginning to analyse the documents.
Google’s Android runs more than 85% of the world’s smartphones, while Apple’s iOS runs 13%, according to research firm IDC. Spokeswomen for Google and Apple didn’t immediately respond to e-mails seeking comment about the WikiLeaks disclosures. Facebook declined to comment.
The CIA also “runs a very substantial effort to infect and control” Microsoft Windows users with its malware, including infecting removable media such as USB drives, WikiLeaks said. The Windows operating system runs more than 90% of desktop computers, according to Net Applications.
A Microsoft representative said in an e-mail: “We’re aware of the report and are looking into it.”
‘Weeping Angel’
In a tactic dubbed “Weeping Angel” in the documents, hackers attack Samsung smart TVs, “transforming them into covert microphones”, according to WikiLeaks. The agency uses the US consulate in Frankfurt as a “covert base for its hackers” covering Europe, Middle East and Africa, according to WikiLeaks.
Samsung didn’t immediately respond to a request for comment.
WikiLeaks said it redacted and removed some identifying information in the content, including tens of thousands of “CIA targets and attack machines” in Latin America, Europe, and the US. The group said it has withheld releasing “armed” cyberweapons until “a consensus emerges on the technical and political nature of the CIA’s programme and how such ‘weapons’ should analysed, disarmed and published”.
The leaked documents show that the government has “deliberately maintained vulnerabilities in the most common devices used by hundreds of millions of people”, Ben Wizner, director of the ACLU Speech, Privacy and Technology Project, said in a statement. “Those vulnerabilities will be exploited not just by our security agencies, but by hackers and governments around the world.”
He said helping companies patch “security holes immediately, not stockpiling them, is the best way to make everyone’s digital life safer”.
- Reported with assistance from Alistair Barr, Dina Bass, Sarah Frier, Jing Cao and Michael Riley