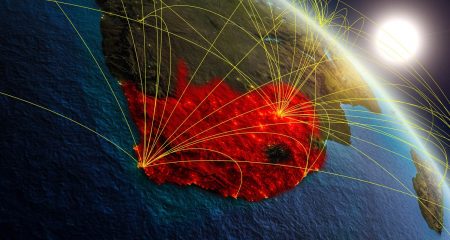
Data has grown exponentially across organisations, increasing the likelihood of them falling victim to cybercriminals whose actions end up impacting shareholder value and business performance. Since the pandemic hit, companies have quickly adapted their technology and approach, with many seamlessly moving their workforce to the home office.
Data has grown exponentially across organisations, increasing the likelihood of them falling victim to cybercriminals whose actions end up impacting shareholder value and business performance. Since the pandemic hit, companies have quickly adapted their technology and approach, with many seamlessly moving their workforce to the home office.
Over the years the role of the chief information security officer (CISO) has undergone significant change. The CISO wears a lot of hats, and the role now goes beyond simply ensuring that the company adheres to security legislation and upskills employees with security protocols to ensuring profitability through safeguarding the organisation’s data.
Just like anyone would ensure the safety of their own home, organisations also need to be treated with care and mindfulness to avoid company turnover values, business registration, credit and financial information landing in the wrong hands.
The latest survey* on CISOs found that in South Africa, 98% of organisations experienced at least one cloud data breach in the past 18 months, while another recent survey± discovered that the average cost of a data breach in South Africa grew to R46-million in 2021. Added to that is the loss to a business’s standing and shareholder confidence.
There are many third parties accessing critical data. Fortunately, CISOs have various options to easily mitigate this risk by creating data-security “safe zones”.
A robust agentless data loss prevention (DLP) solution is a requirement since a lot of data sharing happens between guests, employees and any third parties accessing an organisation’s internal systems. ITsMine’s agentless DLP solution for Maxtec partners is built to protect data from the inside out, differentiating between two attack vectors and managing them automatically. The solution also allows users to safely share data across different devices and locations.
Peace of mind
ITsMine provides CISOs with the peace of mind that comes with knowing no harm can befall the business. Its features alert administrators to improper file use, while also reinforcing the correct behaviours for employees. This powerful agentless DLP solution is an invaluable tool to protect against external and internal threats automatically.
The solution features unique SoftwareMines, acting as the last line of defence. These are dedicated made-up files, planted in sensitive locations adjacent to files that need protection. “Stepping” on a SoftwareMine, including opening, or even tampering the file’s permissions, will immediately send an alert to an organisation’s security team for them to take the necessary steps. The unique, agentless Beyond DLP offering then secures and protects all three phases of digital data, using artificial intelligence, behaviour analysis and deception techniques.
CISOs know the importance of executing data security in an effective way, but also know well how tedious and draining setting policies and classifications can be. ITsMine does this seamlessly on behalf of the team with:
- Continuous discovery of data usage patterns;
- SoftwareMines: decoys deployed in the data sharing safe zones to monitor and control usage of data in these zones;
- Integrated data security training campaigns, increasing awareness of data security within the data security safe zones;
- File GPS: virtual data tagging and tracking of data’s location leaving the safe zone to prevent misuse of a company’s data; and
- File Timebomb: Time-configured voiding of data shared beyond the safe zone.
Unlike many data security solutions, ITsMine’s technology works across Microsoft 365 and Google Workspace cloud environments, and automatically constructs data security safe zones for sharing and collaborating.
The remote workforce is growing daily, and not only owing to the pandemic, as businesses have come to realise that a brick-and-mortar establishment is not always required. However, with this benefit comes the complexity of having to move sensitive data across less controlled environments, making it more vulnerable to a data breach. The need to safeguard sensitive data is a reality that should be planned for by all types of businesses.
Maxtec is proud to offer ITsMine as a powerful agentless DLP solution to all of our resellers. Contact us for more information or to set up a demo. Visit maxtec.co.za/itsmine for more.
Watch: Protecting unstructured data doesn’t have to be a nightmare
*IBM Security, surveyed organisations on the average cost of a data breach in South Africa. ±IDC survey on organisations’ experience with cloud data breach in the past 18 months.
About Maxtec
Maxtec distributes market-leading data security technologies that are trusted around the globe. We empower South African and SADC IT partners with advanced Security Fabric from Fortinet, Intelligent Broadband from Allot, SSL/TLS certification from Sectigo, Network Defence as a Service from Cyglass, Scattered Data Protection from ITsMine, Secure Cloud Backup from Acronis and Vulnerability Remediation from BigFix.
- This promoted content was paid for by the party concerned