Skybox Security has released new findings from the largest cybersecurity benchmarking study of global executives. The research shows that traditional security approaches that rely on reactive, detect-and-respond measures and tedious manual processes can’t keep pace with the volume, variety and velocity of current threats. As a result, 27% of all executives and 40% of chief security officers (CSOs) say their organisations are not well prepared for today’s rapidly shifting threat landscape.
Skybox Security has released new findings from the largest cybersecurity benchmarking study of global executives. The research shows that traditional security approaches that rely on reactive, detect-and-respond measures and tedious manual processes can’t keep pace with the volume, variety and velocity of current threats. As a result, 27% of all executives and 40% of chief security officers (CSOs) say their organisations are not well prepared for today’s rapidly shifting threat landscape.
For full research citations and in-depth analysis, download the report
In summary
- 25% increase in 2021 in material cybersecurity breaches – those generating a large loss, compromising many records or having a significant impact on business operations
- Top four causes of breaches are avoidable, according to cybersecurity researchers
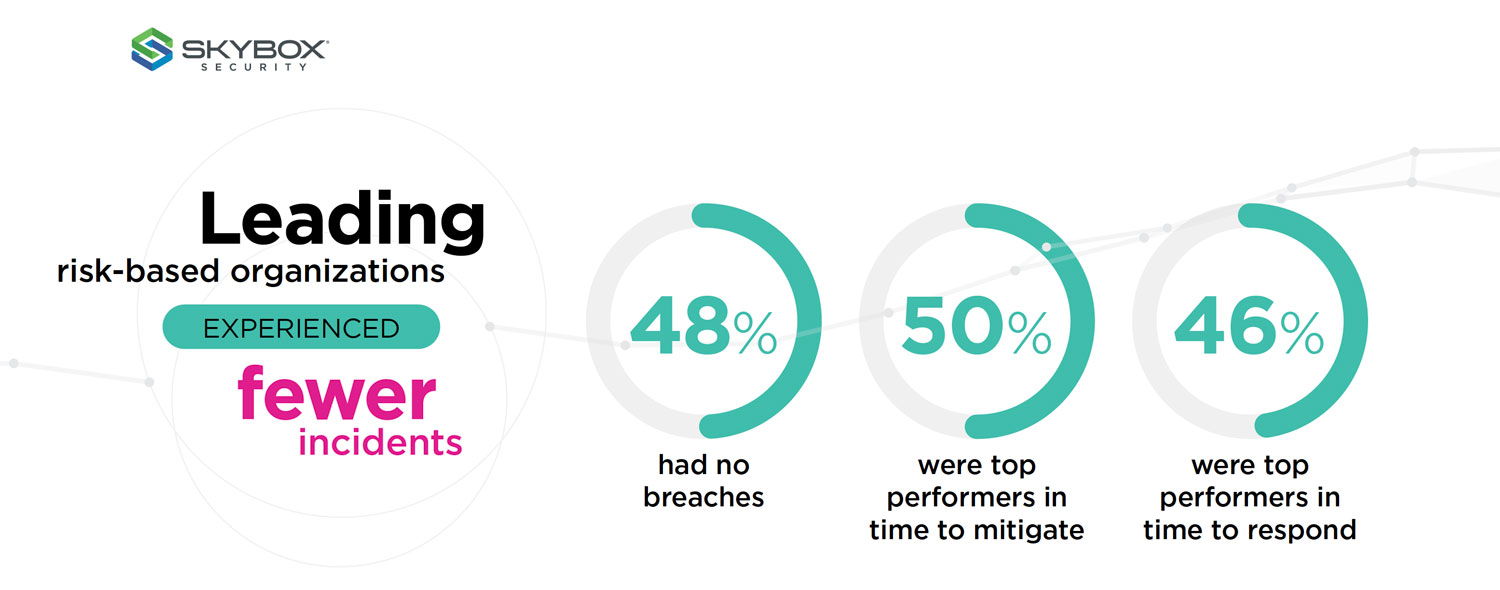
- 48% of organisations with no breaches in 2021 were risk-based cybersecurity leaders
A tipping point
On average, organisations experienced 15% more cybersecurity incidents in 2021 than in 2020. In addition, “material breaches”— defined as “those generating a large loss, compromising many records or having a significant impact on business operations” — jumped 24.5%.
The top four causes of the most significant breaches reported by the affected organisations were:
- Human error
- Misconfigurations
- Poor maintenance/lack of cyber hygiene
- Unknown assets
“What’s notable about this list is that all of these conditions result from mistakes or manual processes inside organisations — which means they are all, in principle, avoidable,” said Ran Abramson, threat intelligence analyst at Skybox Research Lab. “The clear implication is that, however pernicious external threats have become, cybersecurity teams still have the power to repel them. And that’s the good news: with the right practices and tools – including automation to maximise efficiency and get the most out of limited staff – breaches can be prevented.”
Risk-based approach prevents breaches
The study surveyed executives and analysed the cybersecurity investments, practices and performance of 1 200 companies and public-sector organisations in 16 countries and a wide range of industries. It’s the largest cybersecurity benchmarking study with C-level decision-makers ever undertaken. The research findings uncover that conventional cybersecurity approaches are falling short, and organisations that shift to modern, risk-based strategies are more successful in preventing breaches.
Though organisations, on average, saw a significant uptick in incidents and material breaches in the past two years, a distinct subset had few or no breaches at all. So, what sets these exceptional organisations apart? The researchers found that firms with fewer breaches were different from the rest of the pack in two fundamental respects:
- Organisations that prevented breaches ranked higher in cybersecurity progress as measured by the NIST framework. The framework, developed by the National Institute of Standards and Technology, provides guidelines that help companies evaluate and improve their cybersecurity maturity in activities such as detecting and responding to incidents.
- Beyond the NIST framework, organisations with no breaches took what the researchers call “a risk-based approach” to cybersecurity. Forty-eight percent of organisations with no breaches in 2021 had implemented risk-based cybersecurity management strategies. They also performed better in key cybersecurity metrics: 46% were top performers in time to respond to a breach, and 50% were top performers in time to respond.
Looking more closely at the ingredients of a risk-based approach and the specific practices that distinguish risk-orientated organisations from their less proficient peers, the benchmark study found that risk-based leaders excelled in key areas beyond the NIST framework, including:
- Attack surface visibility and context
- Attack simulation
- Exposure analysis
- Risk scoring
- Vulnerability assessments
- Research (threat intelligence)
- Technology assessments and consolidation
“You must take a risk-based approach because you can’t secure everything 100%. There are a lot of questions to ask: what is the business of the business? What does the risk profile look like? What are the threats? What are the implications? And what is the governance process an organisation goes through to make risk-based decisions?” said Gary McAlum, board director at the National Cybersecurity Center.
The business impact of successful risk-based security management — versus the old status-quo, detect-and-respond approach — is measured in this research. By preventing or mitigating breaches, risk-based methods could have saved companies millions annually and prevent untold damage to reputation, customer trust, company morale and market standing.
“The cybersecurity industry is witnessing a paradigm shift in cyber risk. To prevent breaches, chief information security officers must make a strategic shift – from the traditional volume play of identifying vulnerabilities and merely adhering to cybersecurity frameworks to taking a strategic, risk-based view of reducing actual exposure,” said Gidi Cohen, CEO and founder at Skybox Security.
“At the board level, leaders want to understand their risk profile rather than how many vulnerabilities were patched each month. CISOs need to validate and report on how they’re taking measurable, proactive steps to reduce risk systematically and reduce the financial impact a breach could have on their company.”
For full research citations and in-depth analysis, download the report.
About Skybox Security
Over 500 of the largest and most security-conscious enterprises in the world rely on Skybox for the insights and assurance required to stay ahead of dynamically changing attack surfaces. Our Security Posture Management Platform delivers complete visibility, analytics and automation to quickly map, prioritise and remediate vulnerabilities across your organisation. The vendor-agnostic solution intelligently optimises security policies, actions and change processes across all corporate networks and cloud environments. With Skybox, security teams can now focus on the most strategic business initiatives while ensuring enterprises remain protected.
- This promoted content was paid for by the party concerned