 In the last week, Radware’s Emergency Response Team (ERT) has been tracking an emerging global ransom denial-of-service (RDoS) campaign from a group identifying itself as the Russian cyber-espionage group Fancy Bear.
In the last week, Radware’s Emergency Response Team (ERT) has been tracking an emerging global ransom denial-of-service (RDoS) campaign from a group identifying itself as the Russian cyber-espionage group Fancy Bear.
This campaign is similar to the one Radware reported on two years ago. This new group has been distributing extortion e-mails to financial institutions globally for the past week. As of this moment, victims are still receiving ransom notes.
Background
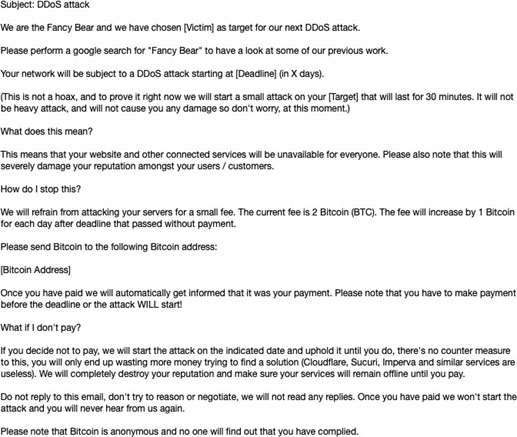
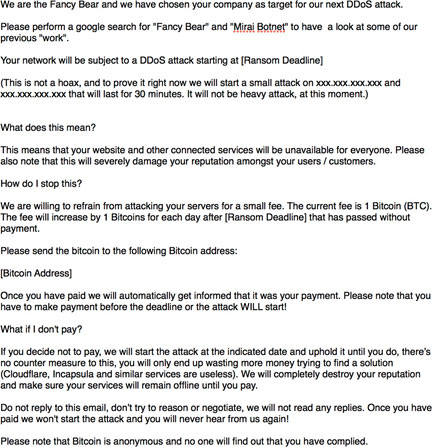
In mid-October 2019, Radware’s ERT began mitigating sample attacks launched by an RDoS group claiming to be Fancy Bear. The extortionists currently behind this campaign attempted to intimidate their victims by using the name of APT28 (Fancy Bear), an infamous cyber-espionage group.
APT28 is a Russian-backed cyber-espionage group that is also known as Pawn Storm, Sofacy Group, Tsar Team and Fancy Bear and is notorious for international hacking related to influence and disinformation operations. RDoS attacks are not the modus operandi of Fancy Bears to date.
Starting in October 2019, almost 2 years after the first major campaign leveraged the name, Fancy Bear began appearing on extortion letters again in a new RDoS campaign. This time, Fancy Bear is requesting two bitcoins, US$17 400 at the time of delivery, with the ransom increasing by one bitcoin every day without payment.
What is an RDoS campaign?
RDoS campaigns are extortion-based distributed denial-of-service (DDoS) attacks motivated by monetary gain. Attacks typically start with the perpetrators sending a letter threatening to attack an organisation — rendering its business, operations or capability unavailable — unless a ransom is paid by the deadline. To validate the threat, attackers will often launch a sample attack on the victim’s network.
This extortion method has grown in popularity every year since 2010 and typically comes in the form of a volumetric DDoS attack. The method was initially introduced by DD4BC and has been replicated by several groups over the years. RDoS group will typical accompany their ransom demand with a short “demo” attack.
Prior RDoS groups were methodical and achieved high success rates. However, today many groups imitate prior tactics and techniques. They spread similar ransom threats using other group names as a form of intimidation with no intention (or limited capacity) of launching an attack.
Targets
Currently, the group claiming to be Fancy Bear is targeting a number of financial services organisations around the world. Attacks have been observed in South America, Africa, northern Europe and parts of Asia. In the note, the attackers list a specific IP address of the victim network and target it with a sample attack. The selection of the specific IP address shows that the attackers are researching targeted network for maximum impact. As of this moment, sample attacks range between 40Gbit/s and 60Gbit/s. No follow-up attacks have been observed.
Attack methods
Most of these DDoS-for-ransom groups that launch attacks are running their own botnet. However, some leverage publicly available stressers to conduct campaigns. When experiencing an RDoS attack from this type of group, expect 40Gbit/s to 60Gbit/s and multiple vectors of attacks simultaneously. A sample attack is likely to last anywhere between 15 minutes to a few hours. In the past, Radware’s ERT has mitigated follow-up attacks that have been persistent and lasted for days. Current attack vectors in this campaign include floods using the following protocols:
- SSDP
- NTP
- DNS
- CLDAP
- WSD
- ARMS
- SYN
- ICMP
The group carrying out the recent wave of RDoS attacks under the name Fancy Bear are currently launching large-scale, multi-vector demo DDoS attacks when sending victims the ransom note. One of the more notable attack vectors from this campaign was the use of Web Service Dynamic Discovery (WSD) protocol, UDP/3702 for amplification. While this attack vector has been known since the beginning of the year, no one publicly spoke about it until the third quarter when details began to slowly emerge that bot-herders had employed a new attack vector into their amplification toolkit.

Another notable attack vector from this campaign is the newly discovered vector that allows attackers the ability to abuse Apple’s Remote Management Service (ARMS) to launch an amplified denial-of-service attack. By sending malicious datagrams to exposed ARMS services on UDP/3283, attackers could gain an amplification factor of 35.5 to 1.
Dealing with a ransom letter
Companies are advised not to pay an extortionist and seek professional assistance for mitigating RDoS attacks. Such a threat usually provokes the need for a scrubbing service, ACL/BGP reconfiguration, as well as the usual DDoS protection essentials to assure uptime and service-level agreements.
Evaluation – is it real or fake?
Although it is almost impossible to determine whether a ransom note comes from a competent, experienced hacker group or an amateur unit, some units emerged under the guise of notorious hacking crews. While these fake groups send e-mails nearly identical to real ransom letters, there are several indicators to distinguish between the two:
- The fake groups often request a different amount of money
- “Real” groups prove their competence; fake groups exclude the “demo” attack
- These groups do not have official accounts, websites or target lists
- When hackers launch real DDoS for ransom attacks, they normally target many companies under the same industry
- Look for suspicious indicators. Is this group known for DDoS attacks?
Effective DDoS protection essentials
- Real-time signature creation: Promptly protect from unknown threats and zero-day attacks. In this current campaign, Radware’s ERT has been able to mitigate all vectors of attacks from the Fancy Bear RDoS group.
- Hybrid DDoS protection: On-premise and cloud DDoS protection for real-time DDoS attack prevention that also addresses high-volume attacks and protects from pipe saturation.
- Behavioural-based detection: Quickly and accurately identify and block anomalies while allowing legitimate traffic through.
- A cybersecurity emergency response plan: A dedicated emergency team of experts who have experience with Internet of things security and handling IoT outbreaks
 For further network and application protection measures, Radware urges companies to inspect and patch their network in order to defend against risks and threats. To know more about today’s attack vector landscape, understand the business impact of cyberattacks or learn more about emerging attack types and tools, visit DDoSWarriors.com.
For further network and application protection measures, Radware urges companies to inspect and patch their network in order to defend against risks and threats. To know more about today’s attack vector landscape, understand the business impact of cyberattacks or learn more about emerging attack types and tools, visit DDoSWarriors.com.
For more information on Radware’s security solutions, contact the Obscure team: e-mail [email protected] or visit the website at www.obscuretech.net.
- This promoted content was paid for by the party concerned




