Organisations are facing an uphill battle in a world where cyberthreats evolve faster than cybersecurity practitioners can keep up. The overwhelming complexity of real-time data and a burgeoning attack surface create a daunting challenge for security teams.
Organisations are facing an uphill battle in a world where cyberthreats evolve faster than cybersecurity practitioners can keep up. The overwhelming complexity of real-time data and a burgeoning attack surface create a daunting challenge for security teams.
Yet the solution lies not merely in data management but also in strategic risk identification and stratification. This is where AI-driven cybersecurity platforms that prioritise risk change the game – offering businesses strategic protection and the advantage of streamlining risk management.
The challenge: cognitive overload in cybersecurity
For firms, monitoring their digital environments can feel like drowning in data. Imagine dashboards displaying billions of messages exchanged every second, relentless external interactions across networks and a slew of critical weaknesses that need immediate attention.
This constant influx of information will overwhelm even the most experienced and skilled security teams. Conventional cybersecurity tools, while adept at generating alerts, often fail to answer the most critical questions – “so what?” and “now what?”.
Learn more at www.snode.com
This cognitive overload inevitably leads to decision paralysis, in which security teams are unable to prioritise amid the noise and end up focusing on symptoms instead of the root causes. This reactive approach can be costly, on the company’s purse and its reputation. Entities need to shift their stance to one that prioritises cyber risk and delivers actionable intelligence.
Identifying the most effective intervention
Vulnerabilities, threats and assets are not all created equal. Treating every alert with the same urgency wastes time and resources. A smart risk-prioritisation approach focuses on understanding which systems or data are most valuable to malefactors. Once this is in hand, they can weigh up the likelihood and impact of each possible attack and pinpoint the most effective intervention to neutralise and proactively manage risks.
Consider this: an AI-powered platform can analyse billions of events in real time, correlating vulnerabilities with potential attack paths for active threats. By isolating a critical vulnerability in an internet VPN that ultimately impacts a high-value internal client database, the platform can recommend a single targeted fix. This allows security teams to spend their limited time addressing the most impactful risks by disabling the attacker’s kill chain.
AI in action: a real-world example
We tested this novel approach on a Southern African telecommunications provider managing millions of transactions and subscribers daily. At any given moment, the company’s systems held between R20-million and R60-million in airtime value within its voucher databases. This airtime isn’t just a number – it’s money in digital form, and if it disappears due to fraud or unsanctioned access, it’s almost impossible to trace. Once leaked into the black market, it becomes an incredibly complex issue.
However, our AI-driven approach processed this massive amount of data on the fly. It analysed millions of transactions, flagged unusual patterns and even isolated a single critical action that required immediate follow-up. In the event the risk was realised, where a fraudulent transaction attempted to siphon off millions of rands worth of airtime, our AI-powered system could recognise the anomaly, contain the threat and proactively mitigate the risk.
This capability – isolating high-risk actions within seconds and presenting actionable insights – is not just innovative but game-changing. It’s not just about technology; it’s about targeted minimisation of financial and reputational risks by ensuring that vulnerabilities in critical infrastructure like telecoms are addressed before they cause any harm.
 Limiting cognitive overload
Limiting cognitive overload
AI-powered platforms transform raw data into actionable intelligence. Instead of reacting to every alert, security teams can focus on the highest-priority risks. This clarity limits cognitive overload and helps security teams make faster and more efficient decisions.
Cybersecurity budgets are already stretched to the max. By prioritising the most critical risks, organisations can allocate resources where they matter most. This limits the chances of costly and embarrassing breaches and avoids budget being wasted on less crucial issues.
Downtime caused by cyber incidents can cripple operations. By proactively addressing vulnerabilities in critical systems, firms can prevent disruptions and maintain trust with customers and stakeholders. Further to this point, all industries face stringent compliance requirements. Risk-based approaches align with regulations like Popia, GDPR and HIPAA, and frameworks like NIST, ensuring companies meet their obligations while minimising exposure to penalties.
The role of AI in driving innovation
AI is the cornerstone of modern risk prioritisation. Here’s how it works:
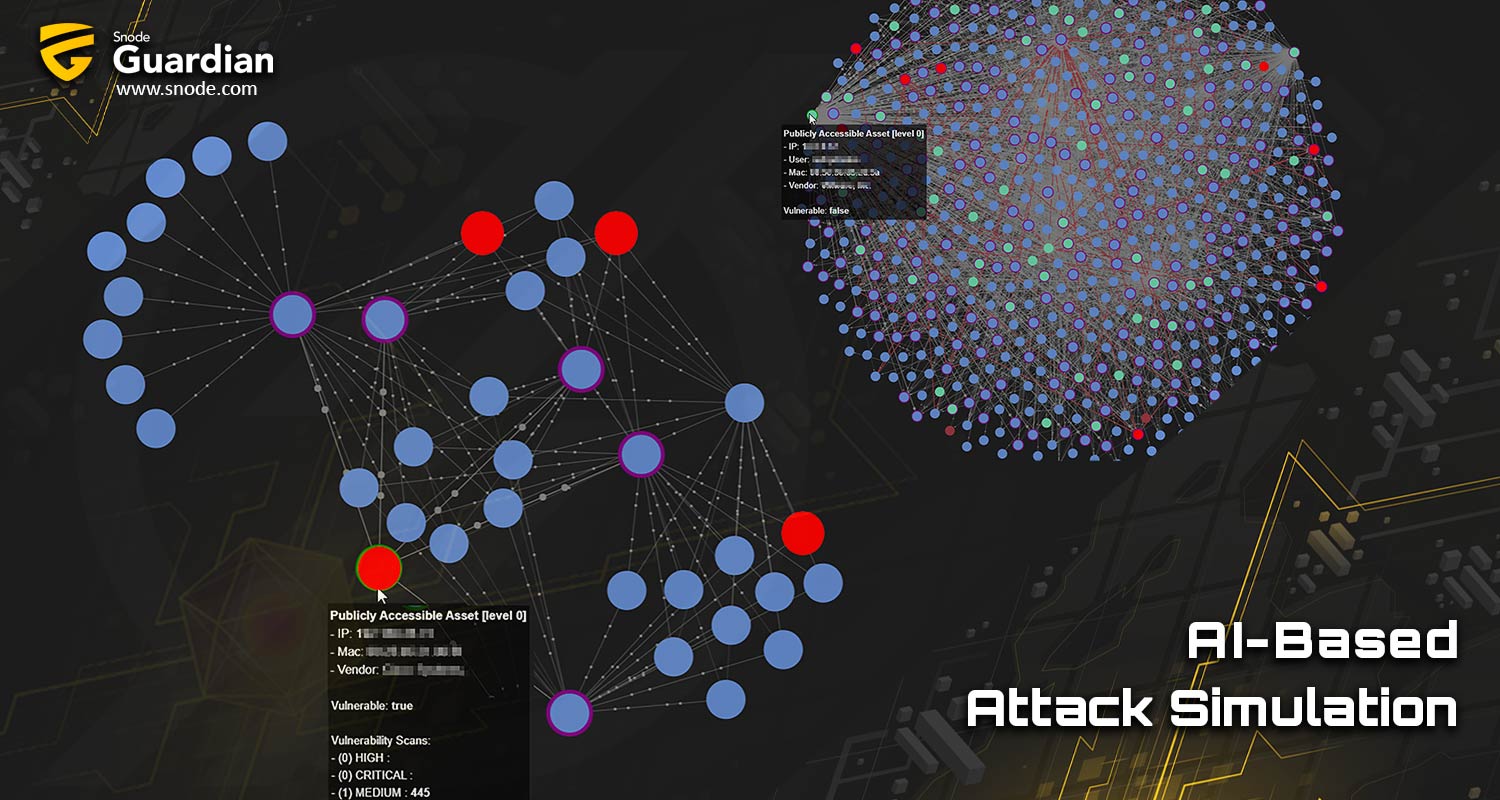
- Correlation and classification: AI algorithms classify related events by attack phase (such as initial access and lateral movement).
- Profiling and cartography: Platforms identify the most critical assets to the business, ensuring targeted protection.
- Digital twin attack simulation: AI creates visual attack paths, showing how vulnerabilities can be exploited – and how to break the chain.
Unlike traditional tools, AI doesn’t just alert – it predicts, prescribes and automates corrective actions. This shift from reactive monitoring to proactive intelligence and automated operations is a giant leap forward in the war against cybercrime.
A smarter, safer future
In cybersecurity, knowing what to protect – and how to protect it – is half the battle. Businesses can shift from firefighting to forward-thinking by leveraging AI to prioritise risk. The result is stronger defences and a more resilient, competitive enterprise.
Sun Tzu once said: “In the midst of chaos, there is also opportunity.” In today’s digital landscape, that opportunity lies in harnessing the power of AI to turn data into intelligence and risks into action.
With a cyber-threat landscape in constant flux, organisations need better, more sophisticated ways to protect themselves. Snode’s approach to cyber threat exposure management (CTEM) incorporates AI, machine learning, active asset management and SOAR, helping businesses proactively defend themselves in the war against exploitation.
Learn more at www.snode.com.
- Read more articles by Snode on TechCentral
- This promoted content was paid for by the party concerned