The US administration is set to release an aggressive new national cybersecurity strategy on Thursday that seeks to shift the blame from companies that get hacked to software manufacturers and device makers, putting it on a potential collision course with big technology companies.
The 35-page strategy, shared in advance with a group of reporters, asserts that software makers must be “held liable when they fail to live up to the duty of care they owe consumers, businesses or critical infrastructure providers”.
“Responsibility must be placed on the stakeholders most capable of taking action to prevent bad outcomes, not on the end users that often bear the consequences of insecure software nor on the open-source developer of a component that is integrated into a commercial product,” according to the document.
The new strategy commits the administration to work with the US congress and the private sector “to develop legislation establishing liability for software products and services”.
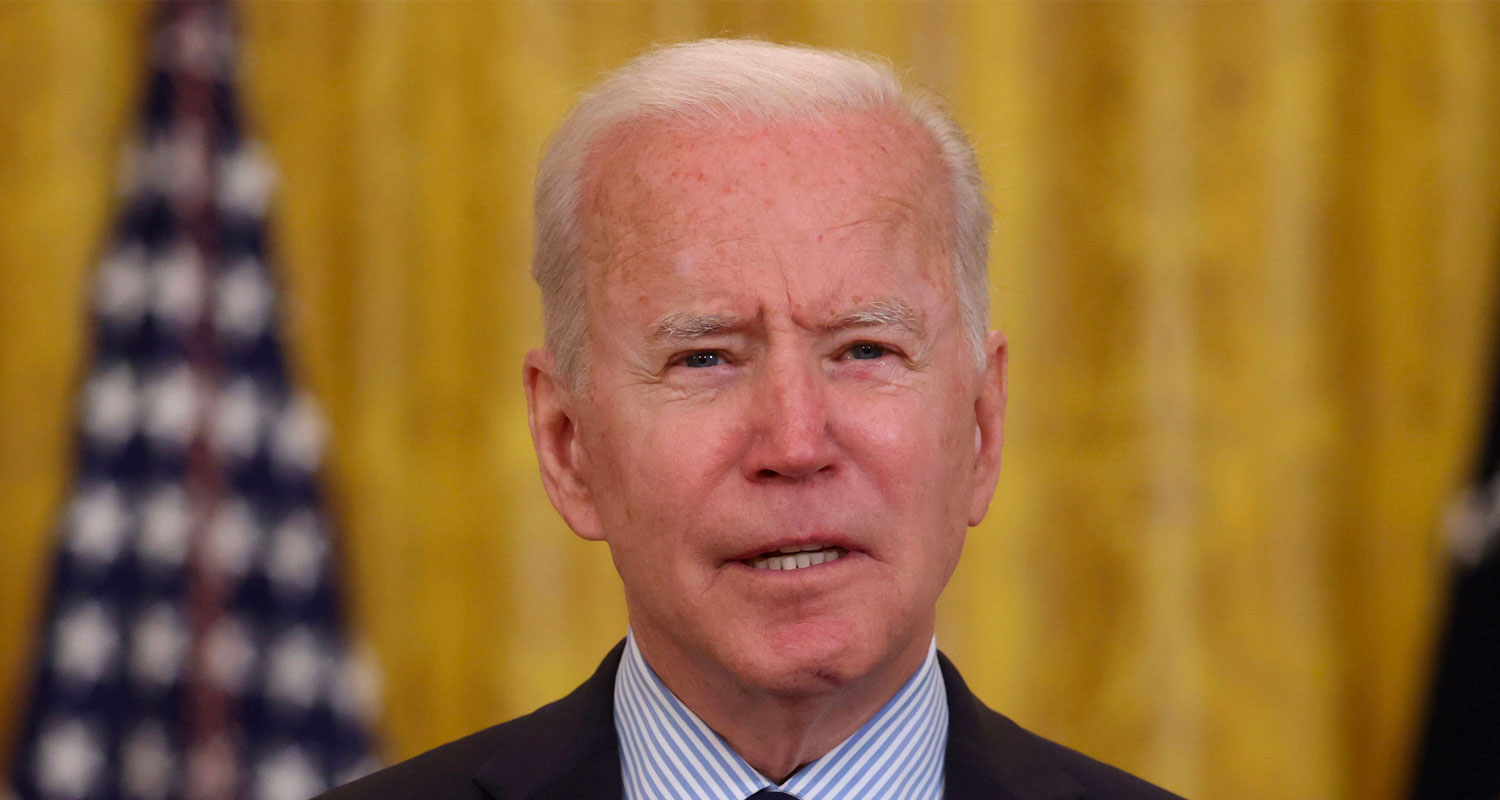
President Joe Biden said in a statement that the strategy “takes on the systemic challenge that too much of the responsibility for cybersecurity has fallen on individual users and small organisations”.
Senior US officials have publicly complained that technology companies, including Microsoft and Twitter, have failed to secure user accounts sufficiently.
Jen Easterly, director of the Cybersecurity and Infrastructure Security Agency, this week fired a broadside over such failings, including flawed code and poor practices, which she said make users susceptible to hacks.
Such an ambitious effort comes despite the failure of the Biden administration to advance legislation in its first two years to rein in the power of the biggest tech companies including Google, Apple, Amazon.com and Meta Platforms.
Legislative action
The White House endorsed such moves although critics said it didn’t push the Democratic senate majority leader Chuck Schumer hard enough. Schumer didn’t put a major tech reform bill up for a vote last year.
A senior administration official, who spoke on condition of anonymity to brief reporters, conceded shifting liability for cybersecurity breaches to software companies would require legislative action and was part of a long-term process that could take as long as a decade. The official added that the administration didn’t expect to see a new law on the books within the next year.
The next presidential election is less than two years away, raising the question of whether the administration can even come close to delivering the most ambitious goal of its new strategy to protect Americans from hackers.
The senior official said that the administration would seek to capitalise on bipartisan support for greater cybersecurity. However, short of legislative action, customers could bring civil claims against software and device manufacturers in a bid to improve security standards and shape market forces, an approach the administration endorses, the official said.
The official said there was room for collaboration with the software industry rather than confrontation. In addition, the administration hopes that its plan will force companies to do better in securing its software to win customers in a competitive marketplace, the official said.
 The administration’s strategy also promises a stronger stance against ransomware, in which criminals encrypt a victim’s files until an extortion fee is paid. (Many attackers now steal files, too, and threaten to post them publicly unless paid.)
The administration’s strategy also promises a stronger stance against ransomware, in which criminals encrypt a victim’s files until an extortion fee is paid. (Many attackers now steal files, too, and threaten to post them publicly unless paid.)
In increasingly aggressive approach to disrupting such groups, the US justice department last year closed down crypto exchanges used by ransomware criminals through the use of sanction, and the FBI earlier this year took down the Hive ransomware group by seizing control of servers and websites used by its members in coordination with German and Dutch officials.
The strategy will also seek to expand minimum cybersecurity requirements for critical infrastructure sectors without additional legislation, likely to be one of its most achievable aims.
Anne Neuberger, deputy national security adviser for cyber and emerging technology, told reporters the administration recognised information-sharing and partnership with industry alone was inadequate to overcome risks to US critical infrastructure and that the administration now needs to “implement minimum mandates”.
She added that the administration had already put in place minimum cybersecurity requirements for pipelines and railways and would announce them for additional industries, though she did not say which ones. — Katrina Manson, with Emily Birnbaum and Courtney Rozen, (c) 2023 Bloomberg LP




