 While many of today’s parents grew up during an age where the Internet and the World Wide Web were just in their beginnings, for today’s kids the virtual world is all but inseparable from the real one. That, of course, presents its own set of challenges for parents to tackle, such as how to teach their offspring proper cybersecurity habits without it seeming like too much of a boring and tedious task.
While many of today’s parents grew up during an age where the Internet and the World Wide Web were just in their beginnings, for today’s kids the virtual world is all but inseparable from the real one. That, of course, presents its own set of challenges for parents to tackle, such as how to teach their offspring proper cybersecurity habits without it seeming like too much of a boring and tedious task.
None is more important than teaching them how to protect their online accounts since they are likely to create quite a few of them. So, teaching them proper password hygiene early on will carry through into their adult lives. But since you are going to be dealing with children, it is important to make the lessons accessible, understandable, fun and easy to remember. To mark World Password Day, which takes place on the first Thursday of every May, we’ll look at some ways you can make password hygiene for kids’ fun.
ESET South Africa CEO Carey van Vlaanderen says: “World Password Day reminds us the importance of teaching our kids to protect themselves online from cyber hackers. We use passwords to secure the most valuable and private parts of our lives; it may be to protect our finances, private document or social media apps. It is really important to always educate and have conversations with your kids about their cyber safety and always making their passwords easier for them to remember, but not easier to be correctly guessed by cyber hackers.”
Passwords are fun, you say?
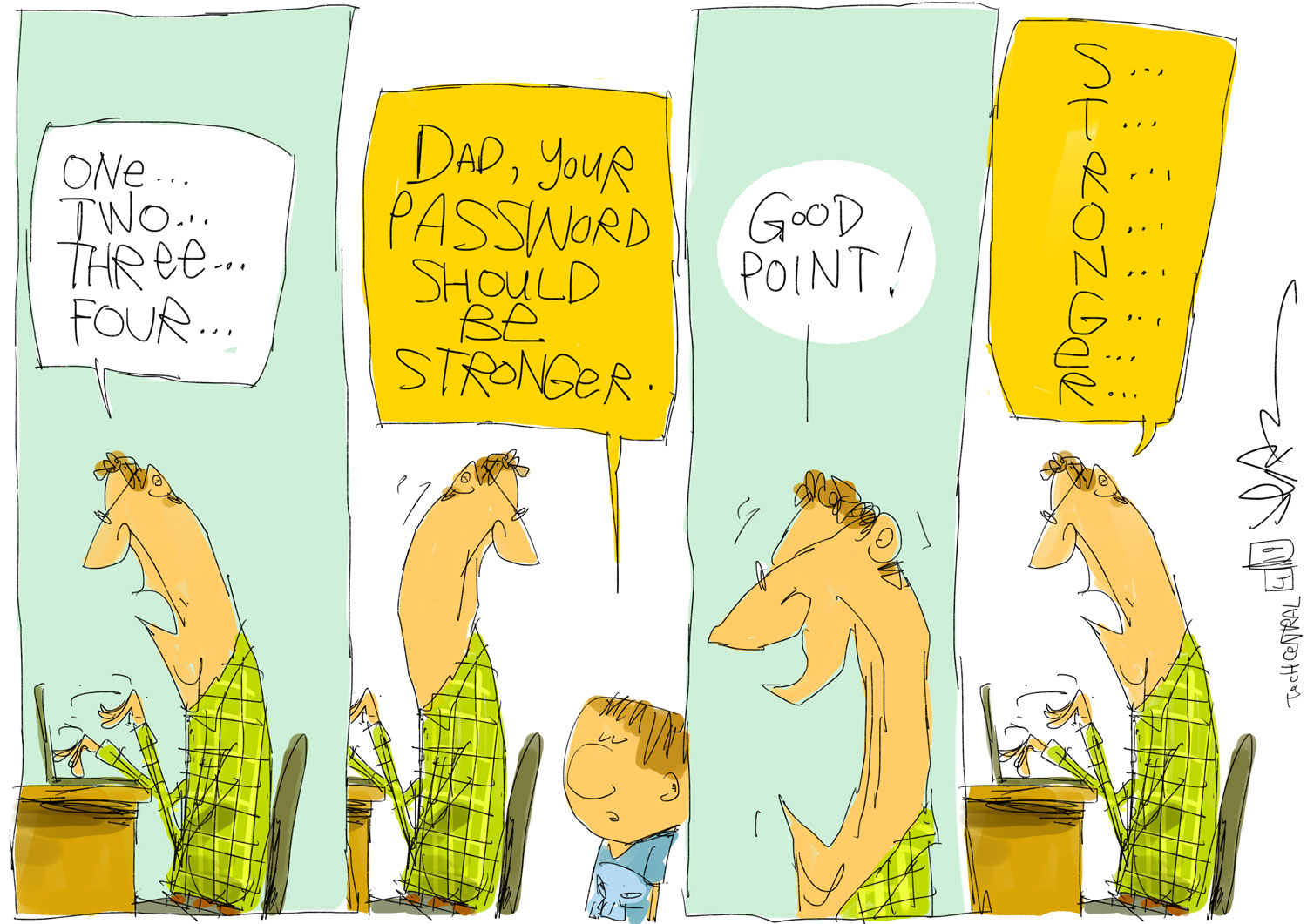
Passwords are the first line of defence keeping anyone unauthorised from having access to your precious data. And while many people might agree that creating a strong and secure password is a no-brainer and everybody should do it, multiple statistics, surveys and breaches have shown that hardly anyone follows this advice. You need not look further than the annual lists of the most common passwords, which are consistently topped by poor password choices such as “12345” and “password”.
Now, should you show the passwords on the list to your kids they would probably call them funny and easy to remember. Funny? Maybe. Easy to remember? Sure. Dangerous? Definitely! But that’s not a habit you want to foster. Instead, you can show them how to avoid the common pitfalls of password creation and teach them how to do it properly with a fun twist. You can start off by telling them that passphrases are a lot safer and you can make a game out of creating one.
This could involve incorporating an inside joke that only the family knows into the passphrase or aspects from their favourite books or films, for example “MasterYodaIs0.66MetresTall!”. As you can see, it includes all the characteristics of a good passphrase – length, a combination of upper- and lowercase letters, special characters and numbers. Alternatively, you could also combine several things they like together, such as their favourite book and food – “HarryPotterAnd5DinoNuggies!”. One key thing to remember to tell your kids is that they should never share their passwords with anyone because passwords should always remain secret.
 Got to remember them all?
Got to remember them all?
Now that you have taught your children how to create a unique and strong passphrase, it is important to keep in mind that throughout their lives they will be creating countless online accounts. And unless you want to burden them with creating a unique one each time and then remembering it, which will be nearly impossible as the passwords pile up, you will have to introduce a solution that will simplify the process.
Enter the password manager, an application specifically designed to store all your login credentials in an encrypted vault and to generate complex passwords for you. This means that your kids will not need to keep creating, memorising or filling out complex unique passwords for their online accounts; the manager will do it for them. All they will need to remember is that one unique master passphrase you came up with together.
Multifactor authentication the undercover spy way
By now your children should have their accounts secure and password management down to a tee. However, to keep their accounts safe, it is necessary to add an extra layer of security. That’s where multifactor authentication (MFA) or two-factor authentication (or 2FA as it is more commonly known) comes in.
One of the most common 2FA factors used is automatic text messages that you receive whenever you try to log into an account. Unfortunately, it’s by far not the safest since mobile numbers can be spoofed and text messages can be intercepted. Therefore, it is better to opt for one of the safer methods, such as an authenticator app or a hardware solution such as authentication tokens.
When it comes to either physical tokens or authenticator apps, it’s easy to dress up their use in a fun way for kids to understand. They have probably seen a cartoon or kid’s movie where the protagonist is a school kid by day and superspy by night. So, you can explain that an authenticator app is a special tool that sends spies a unique code that only they have so they can access sensitive information that is classified as top secret.
In summary
While teaching proper cybersecurity habits to kids may seem like a daunting task, it is nevertheless important to start early, especially in this digitalised day and age. However, by incorporating understandable elements and fun elements it can prove to be a useful and exciting bonding exercise, which will teach your children to remain safe online.
To learn more about more dangers faced by children online as well as about how not only technology can help, head over to Safer Kids Online.
About ESET
For more than 30 years, ESET has been developing industry-leading IT security software and services to protect businesses, critical infrastructure and consumers worldwide from increasingly sophisticated digital threats. From endpoint and mobile security to endpoint detection and response, as well as encryption and multifactor authentication, ESET’s high-performing, easy-to-use solutions unobtrusively protect and monitor 24/7, updating defences in real time to keep users safe and businesses running without interruption. Evolving threats require an evolving IT security company that enables the safe use of technology. This is backed by ESET’s R&D centres worldwide, working in support of our shared future. For more information, visit www.eset.com or follow us on LinkedIn, Facebook and Twitter.
- This promoted content was paid for by the party concerned




