 According to Gartner’s recent Board of Directors Survey, 69% of directors confirmed that the effects of the Covid-19 pandemic and the economic crisis dramatically accelerated digital business initiatives in 2020.
According to Gartner’s recent Board of Directors Survey, 69% of directors confirmed that the effects of the Covid-19 pandemic and the economic crisis dramatically accelerated digital business initiatives in 2020.
However, necessity does not always breed success.
New risk has been introduced, new access points have emerged, and new technologies need to be secured. As a result, the chief information security officer (CISO) has gained new-found influence within the organisation. This is influence that leading CISOs are using to build stronger security programmes. By doing so, they are actively improving their organisations’ security posture while delivering increased business value.
Business-critical role in the new normal
Covid-19 lockdowns have raised the visibility of security as a business issue. CISOs, at the helm of security strategy, now have an unprecedented seat at the boardroom table. According to PwC research, a “majority of CISOs have interacted more frequently with their CEOs (65%) and the boards (50%) during the crisis. In 2019, only 33% of all business and IT executives said that their cyber team communicates effectively with the board and senior executives about cyber risks and adjacent risks”.
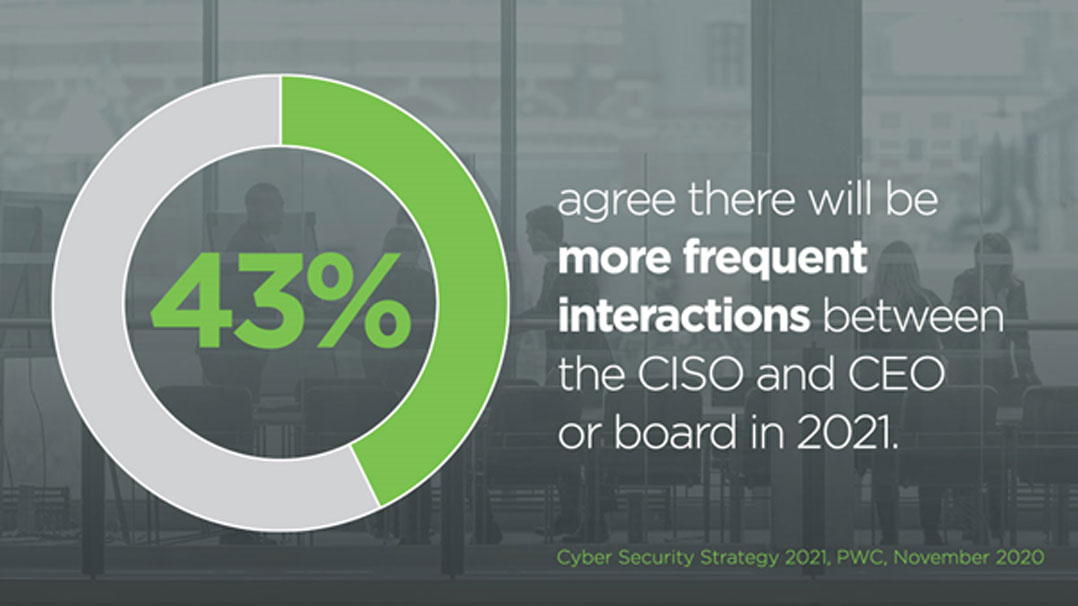 A further PwC report points to two-fifths of C-level executives agreeing that there will be more frequent interactions between the CISO and CEO or board in 2021. The opportunity has arrived for CISOs to embed security into the fabric of the organisation’s business strategy.
A further PwC report points to two-fifths of C-level executives agreeing that there will be more frequent interactions between the CISO and CEO or board in 2021. The opportunity has arrived for CISOs to embed security into the fabric of the organisation’s business strategy.
Six priorities held by forward-leaning CISOs
To make the best use of their newfound seat at the table, CISOs must proactively address the new normal by advocating for the changes necessary to reduce risk. This is a significant task that requires radical security transformation. As well as managing the new complexities and risk introduced by accelerated digital transformation initiatives, organisations need to gain a handle on existing and pervasive risk within their environment. Organisations that are ambitious about the speed and scale of their digitisation plans will be more successful if they collaborate with their security chiefs from the start.
To support business-critical digital transformation initiatives while addressing legacy security issues and improving security posture, CISOs have six key priorities.
1. Retain talent
Digital transformation requires an organisation to attract and retain the security industry’s best and brightest talent. With Cybersecurity Ventures predicting that there are likely going to be 3.5 million unfilled cybersecurity positions globally by 2021, the competition for top talent is incredibly fierce and the challenges associated with retaining staff are pronounced. There are opportunities to turn the tide. Covid-19 is an opportunity for organisations to utilise the new normal of “work-from-anywhere” to provide the flexibility that many employees want and compete for those finite resources.
2. Build resilience
No cybersecurity solution is capable of protecting against every possible form of cyberthreat. Therefore, security programmes need to be able to effectively mitigate damage to systems, processes and reputation, and continue operating once those systems or data have been compromised. They need to address both adversarial threats as well as simple human error.
This includes determining who gains access to the network and how, pinpointing what are the most important assets and services, making sure all critical data is protected, and identifying what controls must be updated to function in a predominately remote workforce.
 3. Accelerate cloud adoption
3. Accelerate cloud adoption
Cloud services are now a prerequisite for operational agility and business continuity. While the CISO must continue to accelerate cloud adoption to support an ecosystem approach to business operations, they must also ensure that connections are safe, secure and compliant, and aligned with data governance policies. Connecting suppliers, customers, shippers and employees is more important than ever to allow all parties to work collaboratively and improve decisions. Now is the time to make hard decisions around replacing legacy technologies, expanding cloud infrastructure and assessing new technologies.
4. Adopt a zero-trust framework
Accelerated digital transformation has also paved the way for an accelerated transformation to a zero-trust framework. In a recent Deloitte poll, over a third of security professionals said that the pandemic has sped up their organisations’ zero trust adoption efforts. Prior to the pandemic, interest in zero-trust architectures was primarily being driven by a recognition that the traditional perimeter-centric security model is not compatible with the way businesses are working today. Now, zero-trust has come to the forefront due to the massive volume of remote workers, putting stress on the infrastructure, particularly VPNs.
5. Increase operational efficiencies
Digital initiatives provide prime ways to improve operational efficiencies. Chief among these is automation, which is fast becoming a hallmark of the smartest and most visionary organisations’ approach to cybersecurity. Companies that can automate routine tasks can free up time for other work that adds more value.
6. Build effective governance
The most resilient organisations have frameworks for consistent prioritisation and mitigation of risk so security teams can stay focused on what matters most. They model and validate compliance requirements across hybrid networks, including those in a business’s supply chain, where data subject to compliance requirements is stored and processed in multiple environments. If improperly managed, the interchange of data between these networks can create an additional opportunity for a compliance failure.
Read about how digitisation is reshaping the role and priorities of the CISO in the report, “Accelerated digital transformation in the post-pandemic era: A catalyst for security transformation”. Download your copy now.
About Gidi Cohen
The author, Gidi Cohen, co-founded Skybox Security in 2002 and has guided the company’s vision and development as the leader in cybersecurity analytics. A respected innovator in the security analytics space, he is a popular speaker at industry conferences worldwide, demonstrating how sophisticated analytics, modelling and simulation, as well as unprecedented network visibility, are used to reduce an enterprise’s attack surface. For more than 10 years he has been committed to empowering security leaders to quickly and accurately prioritise and address vulnerabilities and threats with cutting-edge Skybox solutions.
About Skybox Security
Skybox provides the industry’s broadest cybersecurity management platform to address security challenges within large, complex networks. By integrating with more than 120 networking and security technologies, the Skybox Security Suite gives comprehensive attack surface visibility and the context needed to quickly identify and fix vulnerabilities and security weaknesses. Our analytics, automation and intelligence improve the efficiency and performance of security operations in vulnerability and threat management and firewall and security policy management for the world’s largest organisations. For more information, please visit www.skyboxsecurity.com.
- This promoted content was paid for by the company concerned




