
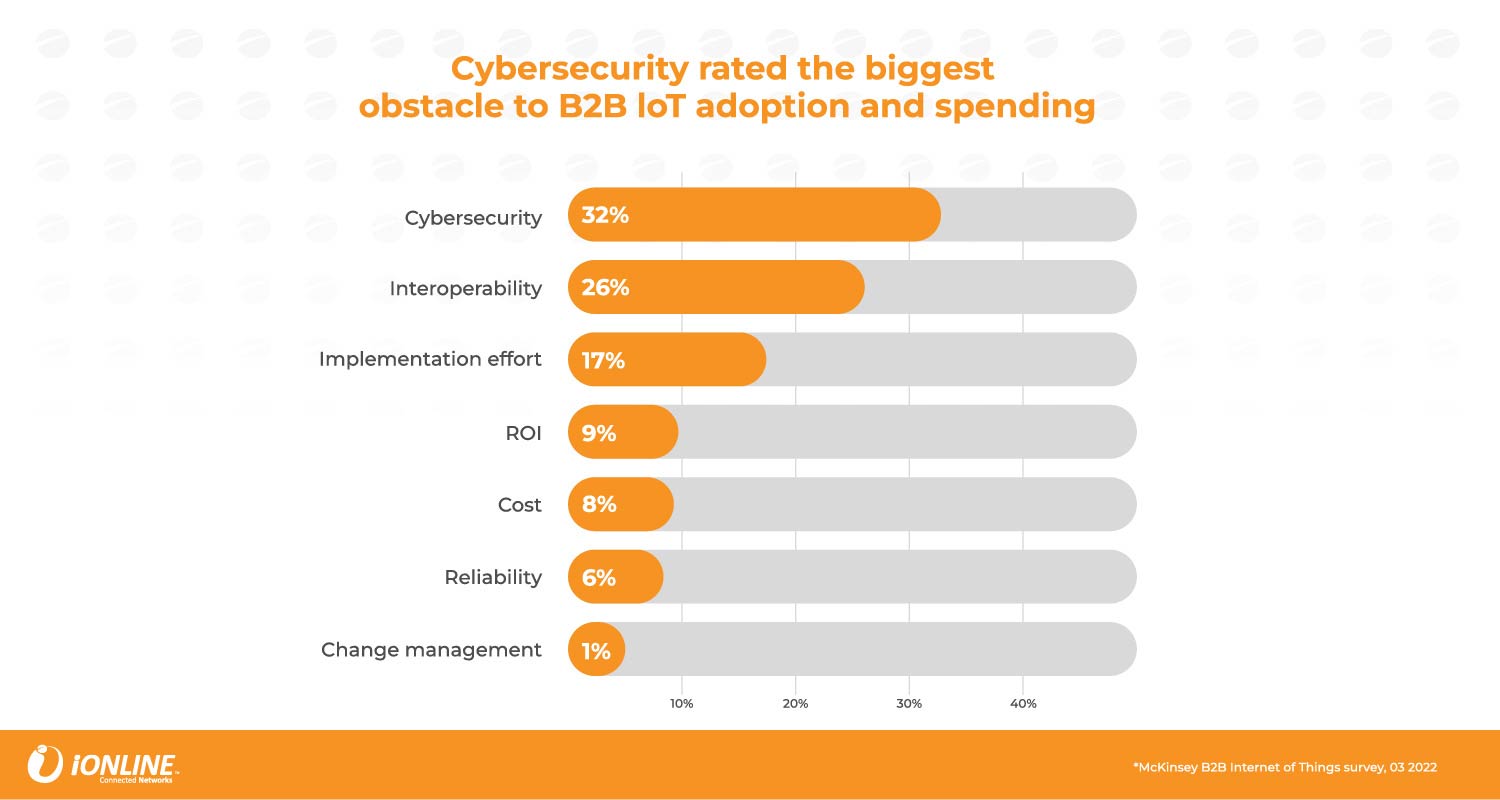
The internet of things presents plenty of opportunities, but almost as many vulnerabilities. While IoT adoption has accelerated in recent years, it still works in largely siloed clusters, across verticals. To unlock its full potential, better integration is needed both within and across these various verticals.
Except cybersecurity is a major obstacle to this integration.
If IoT is to reach its potential as a fully interconnected ecosystem, it and cybersecurity need to work better together.
When risks erode trust
We are now at something of a crossroads, where the IoT can continue to deliver incremental value through these siloed applications, or evolve into a fully integrated ecosystem. Achieving this integration, however, hinges on overcoming several obstacles first, the most crucial being the cybersecurity risks that erode trust among users.
The trouble comes in that cybersecurity is not simply an add-on. Rather, it is a foundational element required to unlock the vast and varied capabilities of IoT.
McKinsey, in its report Cybersecurity for the IoT: how trust can unlock value, notes that poor cybersecurity strategies have created vulnerabilities that make adoption difficult. For example, studies have shown that there exists a significant disconnect between IoT buyers and providers when it comes to the importance of digital trust and privacy.
Visit www.ionlinesp.com to learn more
Key barriers to widespread IoT adoption and integration include:
- Cybersecurity risks undermining trust and integration;
- A lack of seamless interaction among IoT devices; and
- Existing solutions not being sufficiently secure, leading to vulnerabilities and dependency on updates.
Research shows that IoT buyers value digital trust and privacy more highly than providers realise. Siloed decision making compounds this, with contrasting decision-making processes between IoT and cybersecurity departments further stilting adoption.
So, what’s the solution?
Collaboration is the key
Firstly, industry players need to acknowledge the challenges and commit to finding ways to solve them. Then, they need to agree on standards moving forward. This requires collaboration between IoT and cybersecurity solution providers. It also involves improved cybersecurity measures, and new industry standards for both security and interoperability.
David Farquharson, CEO of iONLINE Connected Networks, agrees that the journey towards an interconnected IoT environment is a collective responsibility.
“This collaboration extends beyond technology. It’s about building trust through transparency and open communication about the cybersecurity measures in place,” he says. “When businesses see their third-party providers committed to protecting their data, they are more likely to embrace IoT solutions.”
Farquharson underscores the importance of cybersecurity, saying that as IoT increasingly integrates into critical infrastructure and enterprise systems, so securing devices, networks and systems becomes more urgent.
“Unfortunately, as the IoT landscape evolves, so do the threats,” he says. “Ensuring you have the right expertise at your disposal and have partnered with the right company to deliver the secure solutions you need is how you ensure longevity.”
Together the IoT and cybersecurity sectors can create a resilient ecosystem where users can take full advantage of smart technologies while keeping sensitive data safe. The IoT environment of the near future will comprise billions of connected devices communicating through heterogeneous operating systems, networks and platforms, using cloud-based data storage and cloud-native programming. It’s the seamless experience for which industry players long, and it is this which will boost adoption of IoT.
Where to from here
McKinsey states that if the two worlds of IoT and cybersecurity can successfully converge, we could see IoT spending increase by as much as 40%. This could boost the market value to between US$625-billion and $750-billion by 2030.
“By integrating advanced security features into our IoT connectivity solutions at iONLINE, we transform fragmented systems into a trusted and cohesive connected network that works uninterrupted across industries and use cases,” says Farquharson. “This not only addresses existing vulnerabilities but also sets a foundation for future advancements.”
 The potential is easy to see, he continues. “Without a doubt, the convergence of IoT and cybersecurity will ignite innovation, leading to even smarter and more secure systems that positively impact all areas of life. Organisations that adapt to these changes swiftly and efficiently stand to benefit enormously.”
The potential is easy to see, he continues. “Without a doubt, the convergence of IoT and cybersecurity will ignite innovation, leading to even smarter and more secure systems that positively impact all areas of life. Organisations that adapt to these changes swiftly and efficiently stand to benefit enormously.”
As the IoT landscape continues to evolve, now is the time for organisations to prioritise cybersecurity in their digital transformation strategies. Explore how iONLINE Connected Networks can help you navigate this journey and secure your IoT investments. Visit our website to learn more about our solutions, read our latest insights or book a demo with one of our IoT connectivity experts to unlock the full potential of IoT and drive innovation at scale.
You can follow us on LinkedIn and Facebook, where we share insights, trends, use cases and industry news every week.
About iONLINE
iONLINE Connected Networks is a leading connectivity provider that delivers cutting-edge technology solutions to businesses around the world. Its flagship product is its multi-network-resilient global IoT connectivity solution, an intelligent network switching Sim (eUICC) called FlexiSIM, which connects in 189-plus countries on over 700 carriers.
With offices in South Africa, the UK, the US and Australia, iONLINE is dedicated to providing exceptional customer service and ensuring that its clients remain connected in a constantly changing world. Furthermore, iONLINE is committed to promoting positive change for both society and the environment, reflecting its dedication to corporate social responsibility. Visit www.ionlinesp.com to learn more.
- Read more articles by iONLINE on TechCentral
- This promoted content was paid for by the party concerned




