South Africa is not paying enough attention to the threat future quantum computers could pose to cybersecurity and national key points such as water infrastructure and power stations.
This is according to Noelle van der Waag-Cowling, research fellow at the School for Data and Computational Science at Stellenbosch University, who said with warfare increasingly becoming digital, a clear national quantum defence strategy is needed to ensure South Africa’s national key points are protected as the technology develops.
“The US in 2022 passed its first national instruction that government departments had to start deploying post-quantum cryptography (PQC) – quantum-resistant algorithms that have been tested. We are seeing a lot of talk about it in the EU; China, North Korea and Japan are also focusing on it. Certain governments have already launched their quantum defence programmes. In South Africa, there is no national discussion or programme to get government and industry quantum-ready,” said Van der Waag-Cowling.
The cryptography used to secure digital systems – including telecommunications and banking infrastructure – relies on mathematically hard problems that take traditional computers trillions of computing cycles to solve. An example Van der Waag-Cowling provided is that it would take the Lengau supercomputer, operated by the CSIR, at least 20 years to break current encryption algorithms.
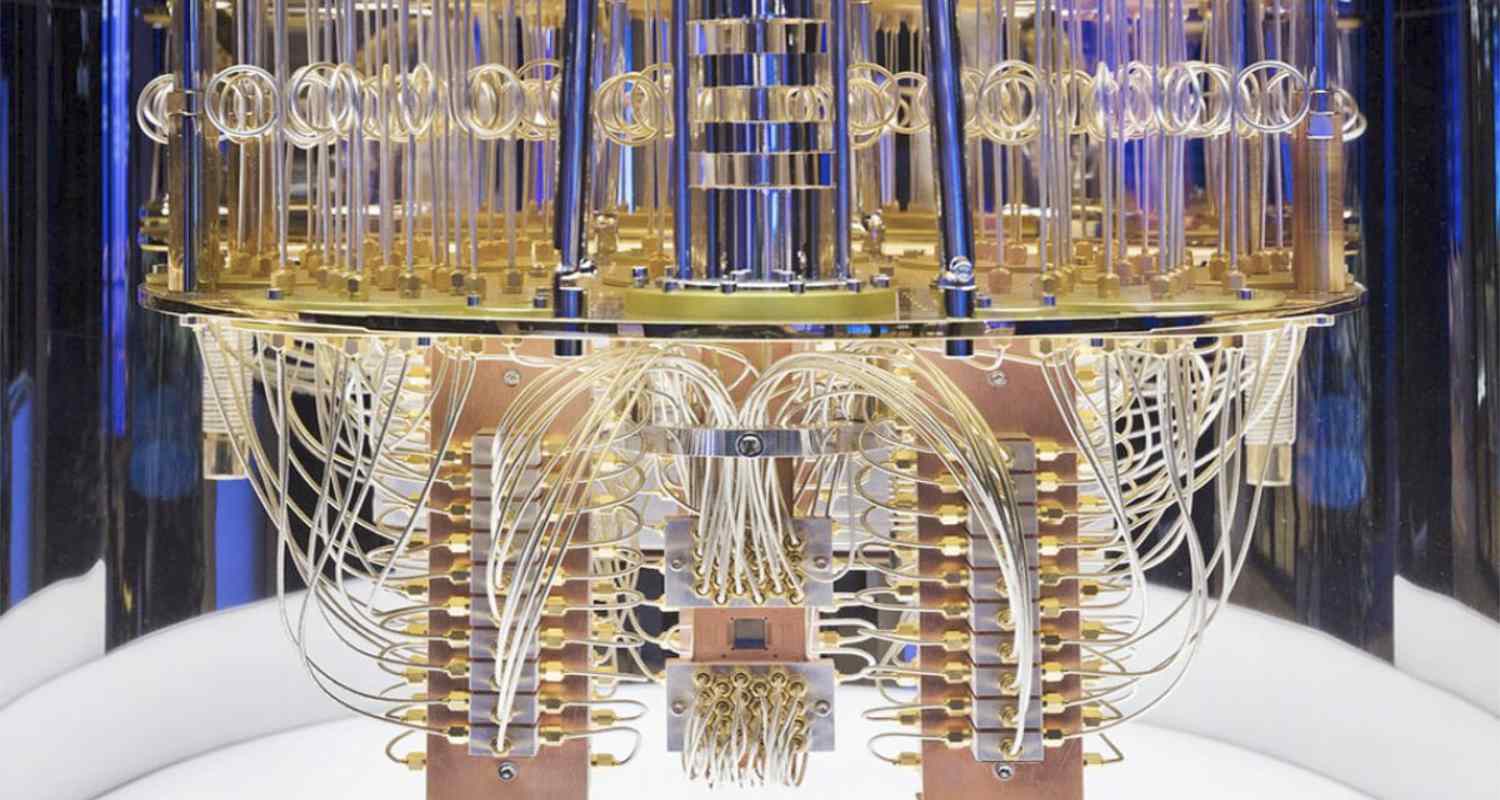
Quantum computers utilise a different paradigm: qubits instead of bits, allowing complex problems to be solved far faster than on classical computers. Whereas a supercomputer could take years, a quantum computer could break an RSA encryption algorithm in just 24 hours. For a bad actor looking to bring down a bank or a power station, this power is dangerous.
“The traditional industrial control systems that you see deployed in places like power stations are notoriously difficult to secure … and quantum computing is just going to make it that much harder,” said Van der Waag-Cowling.
South African Quantum Initiative
PQC standards use the same principle of creating algorithms that are difficult to solve, only the difficulty level is designed to resist both classical and quantum attacks.
Isaac Nape, senior lecturer in quantum photonics at the University of the Witwatersrand, said South Africa does have a good quantum computing strategy, and there are numerous government-funded quantum projects under way with a growing community of academics and researchers contributing to the field.
Read: First quantum cyberattack expected by 2030s – IBM
“The South African Quantum Initiative (Saquti) outlines the national quantum strategy. There are projects ongoing in quantum communications, quantum sensing and quantum computing by the country’s largest universities, all funded by the department of science & innovation,” said Nape.
“In terms of quantum computing, we are not looking at building one. We are thinking: ‘Should quantum computers exist, can we build algorithms that run on them and build custom software tailored to solving problems within our context?’”

One of Saquti’s key project categories looks at how to build telecommunications networks that are resistant to quantum hacking. Nape said the research done at Saquti will eventually filter down into government and industry, advancing innovation and bolstering cybersecurity in the country.
Although it’s predicted that quantum computers will be able to break traditional encryption algorithms, they are not yet at a stage where they can do this. Nape explained that two limiting factors exist. The first is “low qubit capacity”, meaning current quantum computers don’t have enough capacity to perform large computations. The second is that today’s quantum machines are noisy and error-prone, so large computations require significant correction.
These limitations have led to different schools of thought about when quantum computers will be able to break RSA encryption – so called Q-Day. Some believe Q-Day is imminent, while others think it is at least a decade away. Others even think it is multiple decades away.

“Some companies are approaching this with scepticism. But if you look at the road maps of companies in the quantum computing game – the likes of Google, IBM, Microsoft and Amazon Web Services – they are pouring billions into these projects and they predict they will be able to build the hardware to a point where it can perform multiple computations with low error rates in the next decade. So, it’s not a matter of if they will get to it, it’s a matter of when,” said Nape. – © 2026 NewsCentral Media
Get breaking news from TechCentral on WhatsApp. Sign up here.

