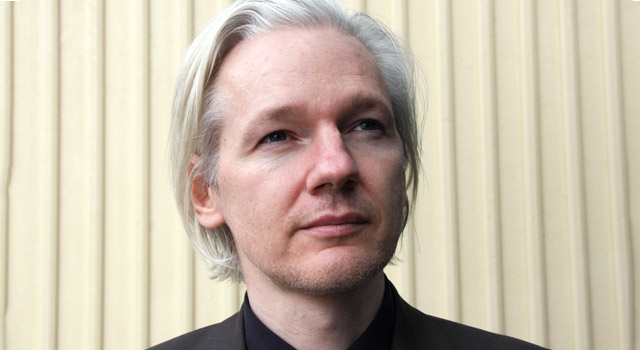
Julian Assange, the founder of WikiLeaks, said the group will work with technology companies to close gaps identified in thousands of Central Intelligence Agency documents it published this week as well as in additional material it has yet to disclose.
Assange, speaking Thursday in a webcast, said he’s interested in helping better secure communications technology after this week’s disclosure of more than 8 000 documents highlighted apparent vulnerabilities in smartphones, televisions and software built by companies including Apple, Google and Samsung Electronics. The disclosures show that the CIA has “lost control” of its “entire cyberweapons arsenal”, Assange said.
Assange, who didn’t name the companies WikiLeaks seeks to work with, said the leaks show how difficult it is for any person or organisation to maintain control of cyber tools.
“If you build them, eventually you will lose them,” said Assange, who remains holed up in Ecuador’s embassy in London. “They are just information. They must be used on the Internet.”
WikiLeaks said on 7 March that it obtained portions of the CIA’s hacking archive and had several hundred million lines of code. The group said it withheld releasing “armed” cyberweapons until “a consensus emerges on the technical and political nature of the CIA’s programme and how such ‘weapons’ should analysed, disarmed and published”.
The CIA, which has declined to say whether the WikiLeaks documents are legitimate, fired back at Assange on Thursday.
“As we’ve said previously, Julian Assange is not exactly a bastion of truth and integrity,” agency spokesman Jonathan Liu said in an e-mail. “Despite the efforts of Assange and his ilk, the CIA continues to aggressively collect foreign intelligence overseas to protect America from terrorists, hostile nation states and other adversaries.”
The WikiLeaks trove, if legitimate, discloses malware, viruses and security vulnerabilities known as “zero days”. It also reveals that the agency has the ability to break into individual devices and intercept messages before they can be encrypted by applications such as WhatsApp, Signal, Telegram and Confide.
The CIA, while not commenting on the authenticity of the documents, said Wednesday that “the American public should be deeply troubled by any WikiLeaks disclosure designed to damage the intelligence community’s ability to protect America against terrorists and other adversaries”.
Republican senator Ben Sasse of Nebraska said on Thursday that Assange should be imprisoned for life. “He’s an enemy of the American people and an ally to Vladimir Putin,” Sasse said in a statement. “Mr Assange has dedicated his life’s work to endangering innocent lives, abetting despots, and stoking a crisis of confidence in the West.”
Assange said during the webcast that he has never been paid by the Russian government or RT, a Russian international television network funded by the Moscow.
Assange, 45, is wanted by the US for exposing classified material and by Sweden over allegations of rape and sexual assault.
Companies including Apple and Google have said many of the vulnerabilities described in the files disclosed by WikiLeaks are old and have already been patched, and that they’re working to fix the remaining ones.
“Our products and software are designed to quickly get security updates into the hands of our customers, with nearly 80% of users running the latest version,” Apple said in a statement similar to those from other technology companies. “We always urge customers to download the latest iOS to make sure they have the most recent security updates.”
A Microsoft representative said on Thursday that “our initial investigation confirmed that most of the information is dated and appears to target older systems. It is likely that a vast majority of the disclosed issues are already addressed in modern systems. We take security issues very seriously and are continuing a deeper analysis.”
As for Assange’s offer to work with technology companies, Microsoft said it hasn’t “yet been contacted” and suggested “our preferred method for anyone with knowledge of security issues, including the CIA or WikiLeaks, is to submit details to us at secure@microsoft com”.
Although US President Donald Trump said “I love WikiLeaks” during last year’s campaign — when it was posting e-mails stolen from rival Hillary Clinton’s campaign chairman — White House spokesman Sean Spicer told reporters this week that there’s a “massive, massive difference” between the two examples. Without confirming the new WikiLeaks documents were genuine, he said: “This should be a major concern to people in terms of the leaks that are coming out, and the desire to get to the bottom of them.” — (c) 2017 NewsCentral Media




