 In 2003, I witnessed the real cost of delayed threat detection. As technical director of cybersecurity at Bankinter, one of Spain’s largest banks, I saw a sophisticated phishing attack unfold in real time.
In 2003, I witnessed the real cost of delayed threat detection. As technical director of cybersecurity at Bankinter, one of Spain’s largest banks, I saw a sophisticated phishing attack unfold in real time.
Despite our tools collecting data diligently, thousands of customer accounts were exposed. Every minute of processing delay gave attackers more time to act. That experience reshaped how I view security: when protecting people’s financial lives, delays of even a few minutes aren’t just inefficient, they’re indefensible.
In 2025, the scale and urgency of this challenge have only intensified.
The CISO’s imperative
As cyberthreats grow more sophisticated and attack surfaces expand, security leaders must turn vast volumes of data into real-time intelligence – before threats strike. Global data creation is set to exceed 180 zettabytes by 2025 (Statista), a ninefold increase since 2020.
This surge offers opportunity for smarter detection, but also risk: critical signals lost in noise can lead to costly breaches. The average MTTD (mean time to detect) for complex attacks is 277 days (IBM report, 2023).
Recent high-profile incidents tell a stark story:
- Capital One Bank took 127 days to detect unauthorised access
- Marriott Hotel discovered its breach after four years
- LastPass failed to detect its initial breach for months
The harsh reality? The security tools we’ve trusted for years just weren’t built for today’s threat landscape, or the threats coming our way tomorrow. They’re leaving organisations vulnerable, and the cost is staggering.
 The cost of data complexity
The cost of data complexity
The impact of complex, inadequate systems extends far beyond immediate incident response costs, which reached US$4.88-million/incident this year – a 10% increase over last year and the highest total ever (IBM). Consider these alarming statistics:
- Eighty-two percent of organisations cite data storage costs as a top security budget concern (IDC), and data storage costs are increasing around 25% annually (IDC)
- Only 25% of enterprise data is used for analytics, while as much as 75% is “dark” and goes unused (Splunk)
- Only 32% of data meets quality standards for analysis (Gartner)
- Some 82% report infrastructure overload from data volume (Cloud Native Computing Foundation)
This paints a clear picture: we’re drowning in underutilised, low-value data.
Legacy observability tools worsen the problem:
- Batch delays: Traditional SIEMs process data in 15-minute to 24-hour intervals – far too slow for cybersecurity.
- High costs: Storing SIEM data can cost $2 000 to $7 000/TB annually (Gartner), an unsustainable model as volumes grow.
- Alert fatigue: Analysts face over 11 000 alerts daily (Forrester, 2023), with nearly half being false positives – leading to burnout and missed threats.
Despite incremental upgrades, most solutions still rely on batch processing and outdated cost models, leaving teams overwhelmed and exposed.
 The technical architecture difference
The technical architecture difference
When we started Onum, we knew solving this required a complete rethink – not just faster tools, but a paradigm shift in how data is handled.
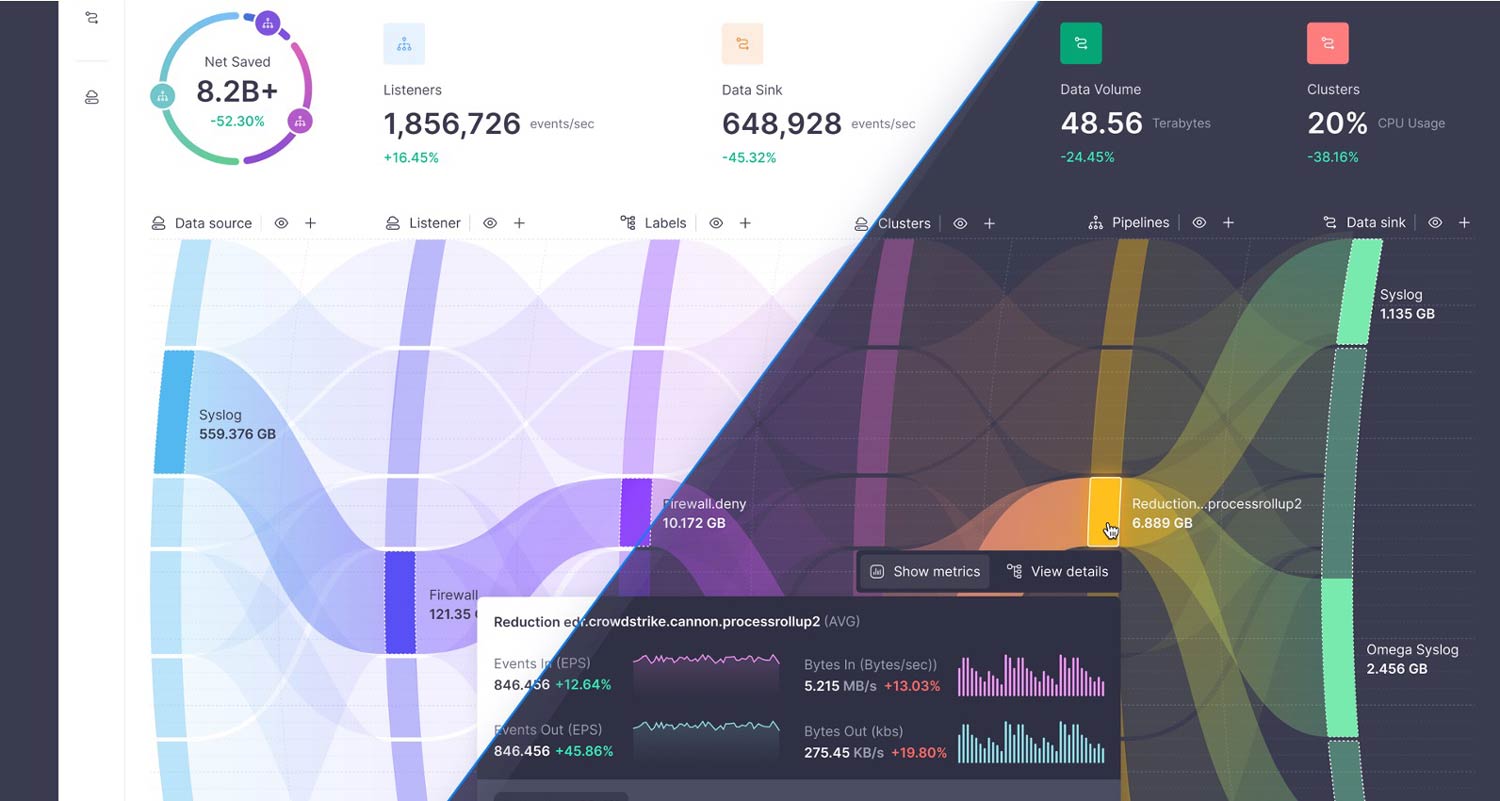
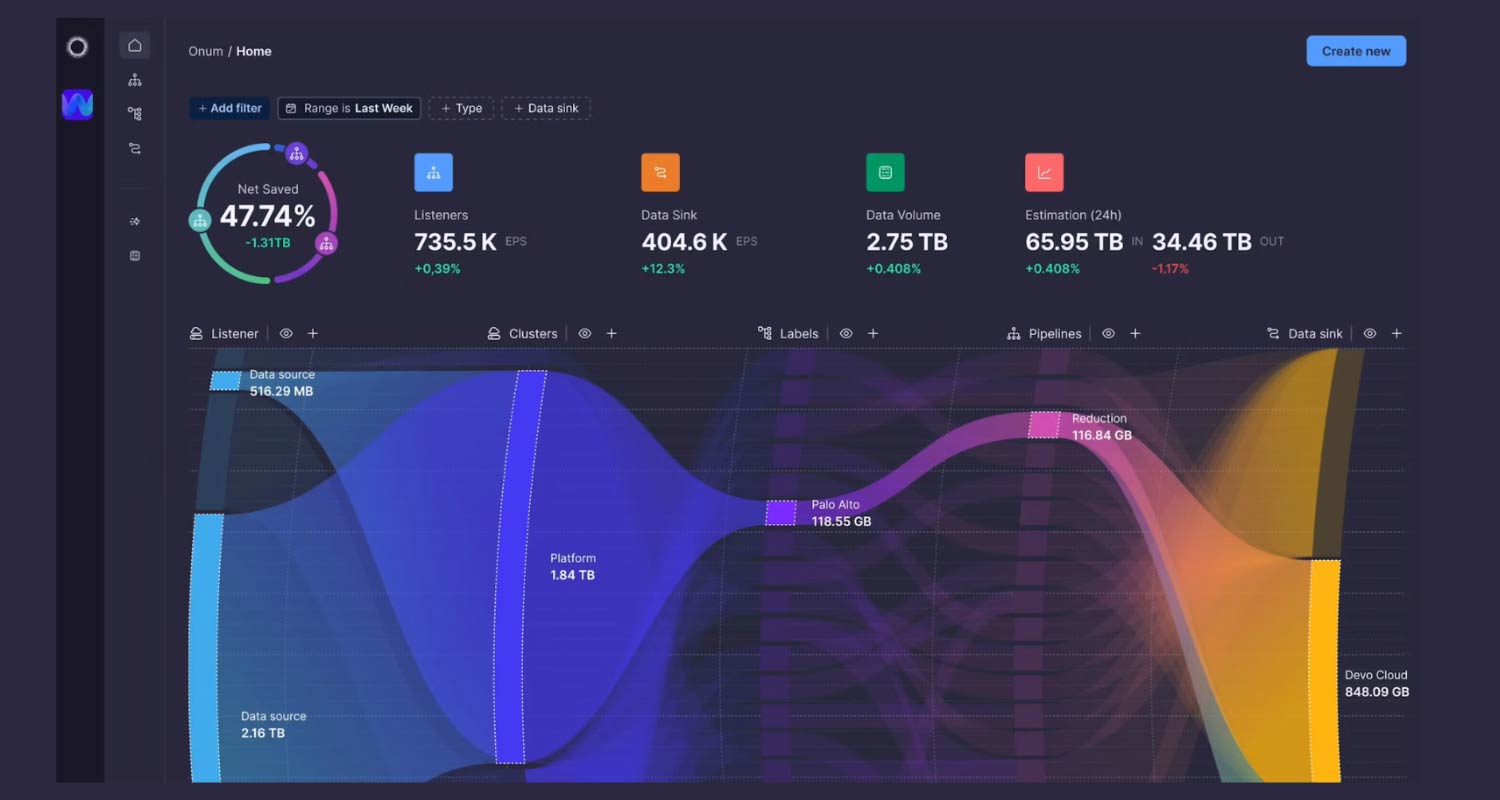
Onum processes and enriches data at the source, helping organisations reduce complexity, outpace ever-growing risks and deliver customer value in milliseconds, not minutes. We’ve reimagined security observability through a modern, stream-based architecture designed for today’s threat landscape and tomorrow’s security challenges. Onum delivers:
- Sub-millisecond data enrichment and analysis through stream processing
- Real-time data classification and prioritisation
- Native integration with major SIEM, Soar and EDR platforms through Rest APIs and dedicated connectors
- Automated response workflow triggers with sub-second latency
- Continuous correlation using machine learning-based threat detection
The platform’s workflows integrate seamlessly with your existing security infrastructure, extending and enhancing current investments rather than replacing them. Onum unlocks immediate, impactful insights because we:
- Reduce overhead and operational bottlenecks: Onum processes data at the edge, as close as possible to its source. Listeners capture and analyse it in real time – before reaching your SIEM – achieving performance up to 5x faster than batch processing, while easing the load on core systems.
- Enrich and transform data in transit: Instead of sending all data to the SIEM, Onum identifies the value of each data field in transit. Only business-critical data goes to analytics tools, while full-fidelity logs are retained for compliance, cutting costs without sacrificing visibility.
- Enable real-time data-backed decisions: Onum uses real-time correlation and smart triggers to detect risks and anomalies as data moves across the wire. This allows for instant remediation and fewer false positives, reducing alert fatigue.
 The cost of waiting: time is the ultimate currency
The cost of waiting: time is the ultimate currency
With cybercrime expected to hit $10.5-trillion annually by 2025, the real question is: can you afford not to modernise? Every minute of detection delay sharply increases risk and potential damage.
Organisations using Onum are seeing:
- A 70% reduction in detection and response times
- A 50% decrease in data storage costs
- Significant improvement in analytics effectiveness
- Enhanced compliance through automated controls
The time for real time is now
That night at Bankinter taught me a critical lesson: in cybersecurity, time isn’t just money – it’s the line between protection and compromise. As attack surfaces grow, waiting for post-incident analysis isn’t just risky – it’s reckless.
About Onum
Onum gives security and platform teams real-time control over the data that powers critical decisions. Built for data in motion, Onum filters noise, enriches signals and moves only the right data to the right tools with zero delay. No lag. No waste. No vendor baggage. Unlike legacy-heavy or observability-only tools, Onum delivers fast, focused control without the overhead. Teams cut costs, accelerate detection and simplify pipelines without sacrificing depth or flexibility. Whether optimising SIEMs or managing multi-cloud telemetry, Onum replaces complexity with clarity, so your data flows cleanly, securely and instantly when it matters most.
Sign up for this upcoming webinar on May 22. And to learn more about Onum, contact our distributor partner, Solid8 Technologies at [email protected].
- The author, Pedro Castillo, is co-founder of Onum
- Read more articles by Solid8 Technologies on TechCentral
- This promoted content was paid for by the party concerned




