 Implementing the Skybox platform, which applies infrastructure context and threat intelligence, allows organisations to improve security policy management and unlock visibility into their entire attack surface that spans IT, operational technology (OT) and hybrid cloud environments. This allows enterprise networking, cloud, security and risk teams to comply with corporate and regulatory policies, reduce misconfigurations, improve cyber hygiene, automate security changes and prioritise remediation of the riskiest vulnerabilities.
Implementing the Skybox platform, which applies infrastructure context and threat intelligence, allows organisations to improve security policy management and unlock visibility into their entire attack surface that spans IT, operational technology (OT) and hybrid cloud environments. This allows enterprise networking, cloud, security and risk teams to comply with corporate and regulatory policies, reduce misconfigurations, improve cyber hygiene, automate security changes and prioritise remediation of the riskiest vulnerabilities.
“Skybox has given us visibility across our network and there’s no other tool that we’ve had in the past that allowed us to do that on a global scale.” – Principal network engineer, IT security company
These capabilities help our customers decrease risk and improve productivity for vulnerability management, audit and compliance processes. But how do these advantages translate to the financial value of deploying the Skybox platform?
 Skybox enabled cost savings and business benefits at a net present value of $2.21-million
Skybox enabled cost savings and business benefits at a net present value of $2.21-million
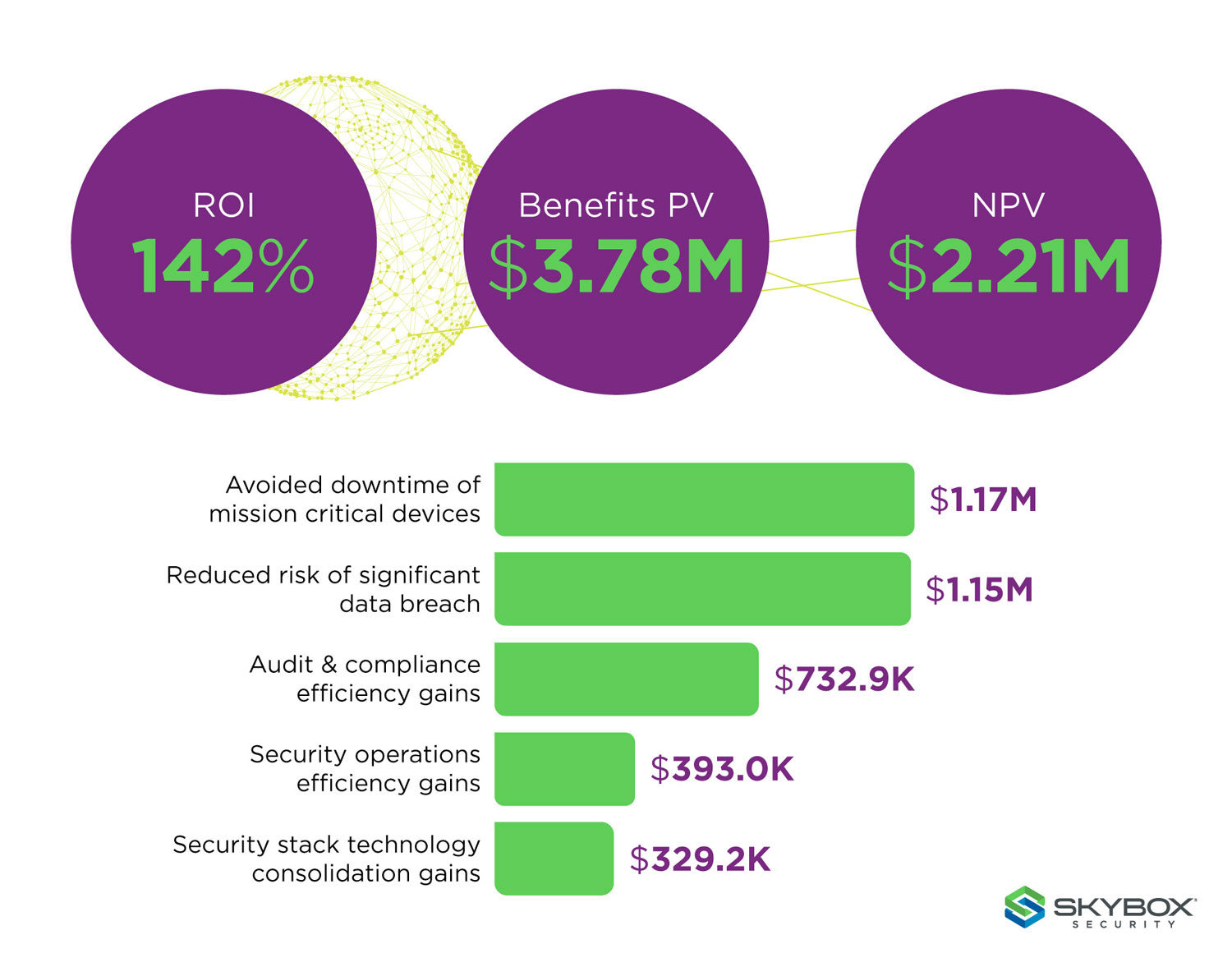
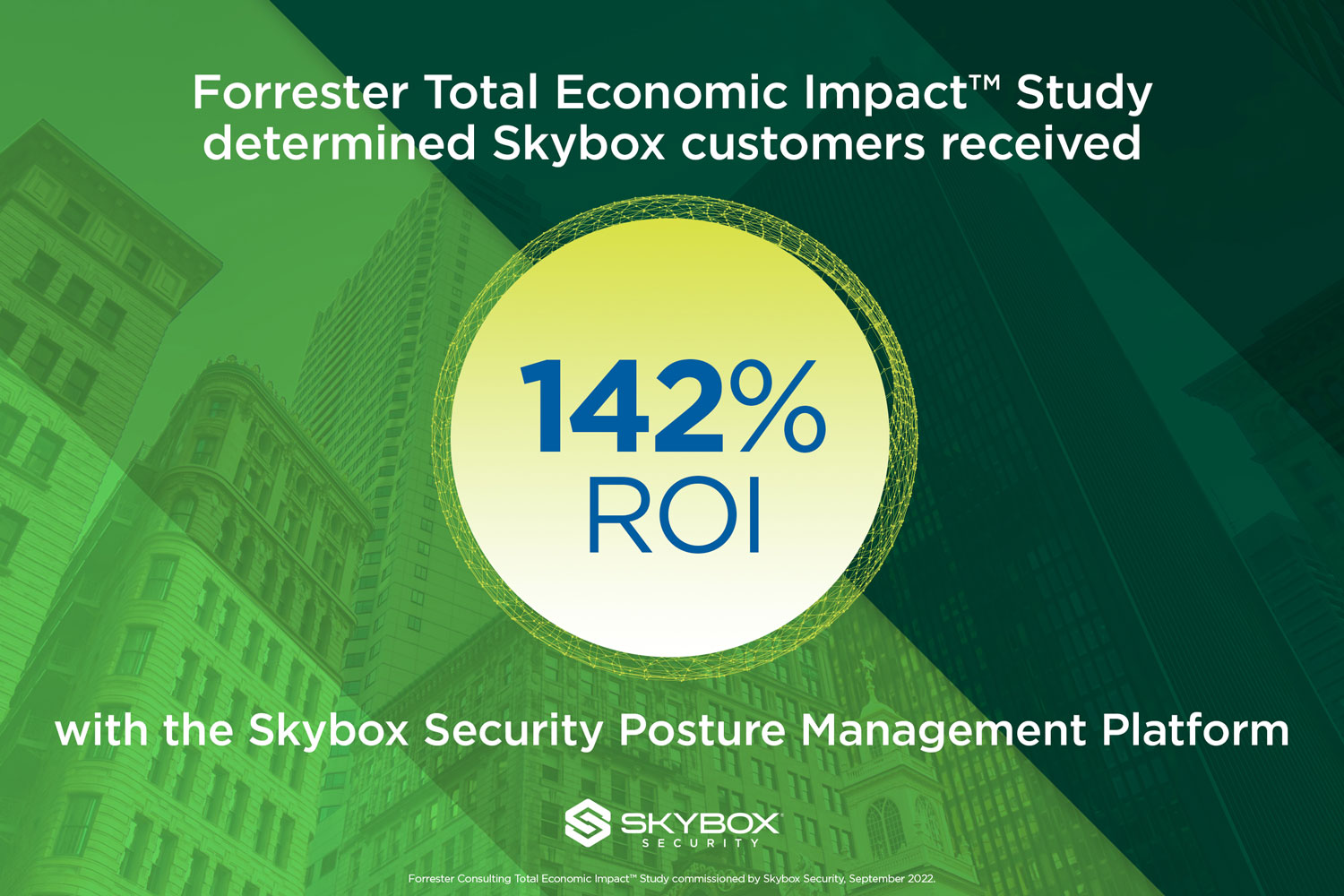
To find out, we commissioned Forrester Consulting to conduct a Total Economic Impact (TEI) study of our Skybox Security Posture Management Platform. The analysis revealed that a composite customer received a 142% return on their investment (ROI) over three years.
Forrester interviewed four real-world Skybox customers across multiple industries and aggregated the insights into a single composite organisation. The resulting organisation reflects the profile of a global enterprise that generates more than $2-billion in revenue annually with 15 000 employees and 30 000 assets. The sheer volume of assets, combined with an explosion of new vulnerabilities (more than 20 000 OT vulnerabilities in 2021 alone), illustrates the core challenges that so many companies face today.
In addition to providing industry-first technology benefits, the Forrester study concluded that organisations deploying the Skybox platform experienced significant economic impact. The representative interviews and financial analysis found that a composite organisation experienced benefits of $3.78-million over three years versus costs of $1.56-million – representing a net present value (NPV) of $2.21-million.
 Skybox reduced the risk of a data breach by 55%
Skybox reduced the risk of a data breach by 55%
By leveraging Skybox’s capabilities to prioritise and remediate exposed vulnerabilities and address compliance concerns, the composite organisation reduced risks from internal and external threats and saw more than a 55% reduction in the risk of significant security breaches from most external and internal threats.
Skybox customers shared that their companies were able to drastically reduce their exposure to significant data breaches resulting from internal and external threat actors. Using Skybox’s capabilities, organisations could better prioritise and understand critical vulnerabilities while addressing compliance concerns on a global enterprise scale. Through increased visibility, interviewees’ companies acted on critical items more quickly across IT and OT functions.
“It was like the Wild West. We have thousands upon thousands or hundreds of thousands of vulnerabilities that show up in scans. What Skybox does is look at vulnerabilities in the context of all the other things in the network to produce a risk assessment, and that’s what allows us to prioritise the vulnerabilities that need to be fixed.” – Principal engineer, IT security company
With a consistent framework for prioritising exposed vulnerabilities, Skybox customers created an internal governance process to centrally review and manage threats across IT and OT environments. This led to a 67% reduction in the time to detect and remediate vulnerabilities for the composite organisation. A manufacturing company saw a reduction from two months to a few days on the IT side of its business and from nine months to as low as two weeks for OT.
Beyond the threat of an external attack, companies were able to leverage network segmentation strategies to limit the risk of internal dangers as well. The principal network engineer at the IT security company shared that they had realised a 200% improvement in their ability to address internal attack vectors. “We’ve been able to use Skybox as a tool to limit movement once a threat is inside the network, to limit where it can go.”
Skybox platform enables technology consolidation
Another interesting outcome of the study was the opportunity for companies to consolidate the technologies within their security stack, leading to significant gains. After implementing the Skybox platform, customers were able to decommission or downgrade other regional or enterprise tools related to vulnerability, firewall and network policy management as well as reporting and analytics toolsets. The composite organisation yielded a projected three-year, risk-adjusted total present value of $329 200.
Making the business case for security posture management
The business impact of successful risk-based security posture management — versus the old status quo, detect-and-respond approach to cybersecurity — is hard to overstate. By preventing or mitigating against breaches, risk-based methods and integrated security posture management can save companies many millions of dollars per year and prevent untold damage to reputation, customer trust, company morale, market standing and competitiveness. By improving efficiencies and reducing workloads, automated risk-based solutions like ours can help you trim costs while accomplishing more — boosting productivity in a time of tight resources and economic instability.
 Contact sales to learn how Skybox can reduce your cyber risk while also saving you time and money. Talk to an expert.
Contact sales to learn how Skybox can reduce your cyber risk while also saving you time and money. Talk to an expert.
About Skybox Security
Over 500 of the largest and most security-conscious enterprises in the world rely on Skybox Security for the insights and assurance required to stay ahead of dynamically changing attack surfaces. At Skybox, we don’t just serve up data and information. We provide the intelligence and context to make informed decisions, taking the guesswork out of securely enabling enterprises at scale and speed. Our security posture management platform delivers complete visibility, analytics and automation to quickly map, prioritise and remediate vulnerabilities across your organisation. The vendor-agnostic platform intelligently optimises security policies, actions and change processes across all corporate networks and cloud environments. With Skybox, security teams can now focus on the most strategic business initiatives while ensuring enterprises remain protected.
- This promoted content was paid for by the party concerned