As cyberthreats grow in scale and sophistication, businesses are realising that cybersecurity is no longer just a technical requirement but a strategic necessity. Yet, for many small and mid-sized businesses (SMBs), the challenge isn’t just choosing the right tools. It’s about having the skills, support and ecosystem needed to use those tools effectively.
This is driving a shift in how cybersecurity solutions are positioned and delivered. Increasingly, success depends on a combination of technology, education and strong channel partnerships. In Africa, this is where Avast Business, together with Avert IT Distribution, is creating meaningful impact.
Beyond traditional security
For years, endpoint protection has been seen as a reactive measure – software that detects and blocks threats after they appear. While this remains essential, it’s no longer sufficient in a world where ransomware, phishing and zero-day attacks are constantly evolving.
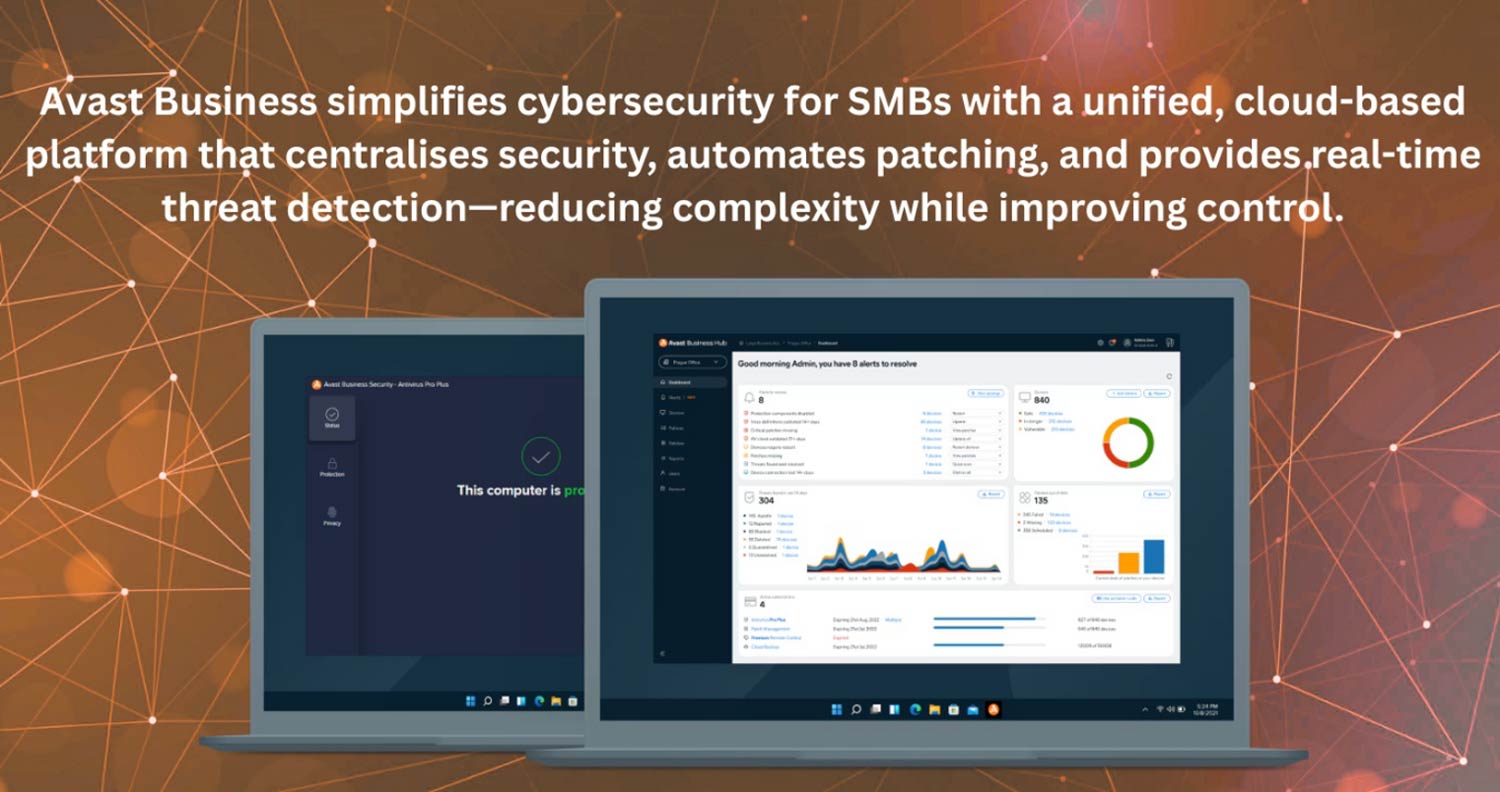
Avast Business addresses this challenge through a unified, cloud-managed platform that brings together multiple layers of protection. From next-generation antivirus and patch management to remote access and backup, the platform is designed to simplify security without compromising on capability.

But what’s increasingly setting solutions apart is not just what they protect – but how they enable users.
Drawing on educational initiatives such as those found in Avast’s academy-driven resources, the focus is shifting towards cybersecurity awareness and skills development. Businesses are being encouraged to understand the “why” behind security practices, not just the “what”.
This approach helps organisations reduce risk proactively – by addressing human behaviour, which remains one of the most common causes of security breaches.
Simplifying security in a complex world
One of the biggest challenges facing SMBs today is the growing complexity of IT environments. Multiple tools, fragmented systems and limited visibility can create gaps that attackers exploit.
Avast Business addresses this through an integrated platform approach. By consolidating key security and management functions into a single solution, businesses can reduce complexity while improving control.
This includes:
- Endpoint protection powered by advanced threat detection
- Patch management to eliminate known vulnerabilities
- Secure remote access for IT support
- Backup and disaster recovery for business continuity
The result is a more streamlined security posture – one that is easier to manage and more resilient against modern threats.
Building a culture of cybersecurity
Even with the best technology in place, human behaviour remains a critical factor. Phishing attacks, weak passwords and unsafe browsing habits continue to expose organisations to risk.
This is why education and awareness are becoming central to cybersecurity strategies. By equipping users with the knowledge to recognise and respond to threats, businesses can significantly reduce their attack surface.
Avast’s emphasis on learning and skills development complements its technology stack, helping organisations build a culture of security from within.

Closing the skills gap
Across many African markets, a shortage of specialised cybersecurity skills continues to be a major barrier. SMBs often lack dedicated security teams, relying instead on general IT support or external service providers.
Avast Business is built with this reality in mind. Its cloud-based management platform allows administrators and managed service providers (MSPs) to deploy, monitor and manage security across multiple environments from a single interface.
Automation plays a key role here. Features such as automated patching and real-time threat detection reduce manual workload while ensuring vulnerabilities are addressed quickly. This makes enterprise-grade security accessible even to organisations with limited resources.
However, technology alone cannot bridge the skills gap. This is where the channel – and specifically distribution – becomes critical.
Avert IT Distribution: enabling the channel across Africa
While technology is critical, successful adoption depends heavily on local support, market understanding and partner enablement.
Avert IT Distribution, the preferred distributor for Avast in Africa, provides the foundation partners need to succeed. With a strong channel-focused model and extensive regional experience, Avert IT Distribution delivers:
- Competitive pricing and flexible licensing options
- Technical support with fast response times
- Partner onboarding, training and certification programmes
- Marketing support to help drive demand
With a network of hundreds of resellers and MSPs, Avert IT Distribution has built a robust ecosystem supporting cybersecurity, backup, remote management and network security solutions.
Importantly, Avert IT Distribution goes beyond product supply – actively helping partners develop managed service offerings and build sustainable, recurring revenue businesses.

From resellers to trusted advisors
This partner-first approach is enabling a broader transformation within the IT channel. Resellers are no longer simply selling licences – they are evolving into service providers delivering ongoing value.
By leveraging Avast Business solutions, partners can offer:
- Managed endpoint security
- Continuous monitoring and threat response
- Data protection and recovery services
- User awareness and training initiatives
This shift towards managed services is particularly important in Africa, where businesses are increasingly looking for outsourced expertise to manage complex IT environments.
With the backing of Avert IT Distribution, partners gain not only access to technology but also the tools and knowledge needed to build scalable service models.
Take the next step
Resellers, MSPs and enterprise buyers looking to expand their cybersecurity capabilities can engage directly with Avert IT Distribution for:
- Avast Business licensing and pricing
- Technical training and partner enablement
- Sales and marketing support
📞 Johannesburg: +27 (0)10 007 4430 📞 Cape Town: +27 (0)21 007 2655 📧 Email: [email protected]
- Read more articles by Avert IT Distribution on TechCentral
- This promoted content was paid for by the party concerned