It has been a bad year for Western intelligence agencies. Being front-page news every week for months at a stretch is not ideal when your business is secrecy. But, whatever the supposed threat to national security, the recent orgy of revelations is a healthy release of toxins.
It has been a bad year for Western intelligence agencies. Being front-page news every week for months at a stretch is not ideal when your business is secrecy. But, whatever the supposed threat to national security, the recent orgy of revelations is a healthy release of toxins.
Both the US’s National Security Agency (NSA) and the UK’s Government Communications Headquarters (GCHQ) have overstepped the boundaries of justice and common sense.
The most recent revelation is perhaps the most shocking: the NSA has spent the past decade sabotaging and undermining the encryption infrastructure on which all private communication over the Internet relies. In the same week, Der Spiegel, a German news magazine, revealed that the NSA and GCHQ have also cracked the codes that protect smartphones.
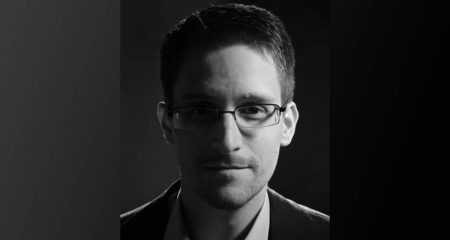
We know this only because Edward Snowden, a former contractor at the NSA, had the courage to leak hundreds of classified documents to the press. Armed with this evidence, the Guardian revealed in June that the NSA has been collecting the phone records of millions of Americans since April this year.
The NSA compelled Verizon, one of the country’s largest telecommunications service providers, to hand over these records using a court order obtained from a secret federal court set up under the Foreign Intelligence Surveillance Act (Fisa). The act, originally passed in 1978, was amended in 2008 to grant broad powers to the US government’s executive agencies (such as the NSA) to surveil anyone suspected of involvement in terrorism.
The NSA is not allowed to collect data on American citizens, or even anyone on American soil, but the documents leaked by Snowden prove otherwise. They detail how NSA agents broke privacy laws thousands of times over a two-year period.
On 6 June, the Washington Post broke the news of an NSA programme codenamed Prism. The programme aims to coerce the world’s largest Internet companies into handing over the private data of any users deemed suspicious by the NSA. The programme has already met and exceeded its original targets.
Then, on 18 August, British police detained and questioned David Miranda, a Brazilian national, at Heathrow Airport. New terror laws allowed them to hold Miranda for nine hours without charging him. His crime? His relationship with Glenn Greenwald, one of the Guardian journalists behind the revelations about the NSA and GCHQ.
This blatant intimidation did not work. Last week Greenwald, with colleagues at both the Guardian and the New York Times, published an exposé of the NSA’s reckless intervention in the Internet’s encryption systems.
So, a quick recap: these agencies now have the power and the means to collect whatever data they see fit, including everything from phone records and e-mails to Facebook messages. All they need do is apply to their secret court for a secret order. Although rules exist to protect their own citizens, these are frequently ignored.
They can detain anyone they like without charge and without just cause. They can sabotage any technology that stands in their way, regardless of the collateral damage it may cause to millions of legitimate users.
When did the organs of democracy and freedom change places with the Gestapo?

Shaken by terror attacks on New York and London, the self-appointed guardians of the free world have unleashed their hounds. The time has come to pull on their chains.
Fisa, and Britain’s terror laws, should be reviewed and amended, if not repealed. The NSA and GCHQ have proven that, given enough rope, the spies will hang us all.
But we must resist the urge to put any blame on technology. Technology is a tool; it has no morals or urges or biases. Were they able to do so, the NSA and GCHQ would shut down the entire Internet for good. We must not let them undermine the greatest invention since the printing press.
The answer is not to roll back technology — the answer is to roll forward democratic participation. The Arab Spring, however muddy it has now become, used social media to mobilise millions of people around a just cause.
Let us use the Internet to rally around our freedom to communicate in privacy. Let us tell our governments, loudly and often, that to sacrifice our freedoms for the sake of security is a terrible bargain. For that is a bargain born of fear, not sense, and if we accept it, then the terrorists will already have won. — (c) 2013 Mail & Guardian
- Alistair Fairweather is chief technology officer at the Mail & Guardian
- Visit the Mail & Guardian Online, the smart news source