If you think Eskom’s load shedding causes disruptions, there’s potentially an even bigger problem for the economy waiting in the wings – a technology outage caused by a cyber attack. The very functioning
Browsing: In-depth
As famously contrarian investors, the one stock Allan Gray might be thought least likely to hold is Naspers. Besides being the flavour of the market, the counter is trading on multiples that most value
DStv parent MultiChoice did not force the SABC to agree not to carry its free-to-air channels on broadcasting platforms that use encryption and a clause to this effect in a channel supply agreement
Many millions of people throughout the world will illegally download the fifth season of Game of Thrones, which began screening around the world, including in South Africa, this month. Legally
In the past three months, I’ve visited three francophone countries — Côte d’Ivoire, Cameroon and Mali — and talked to those involved in the start-up ecosystem in each country. The most developed of
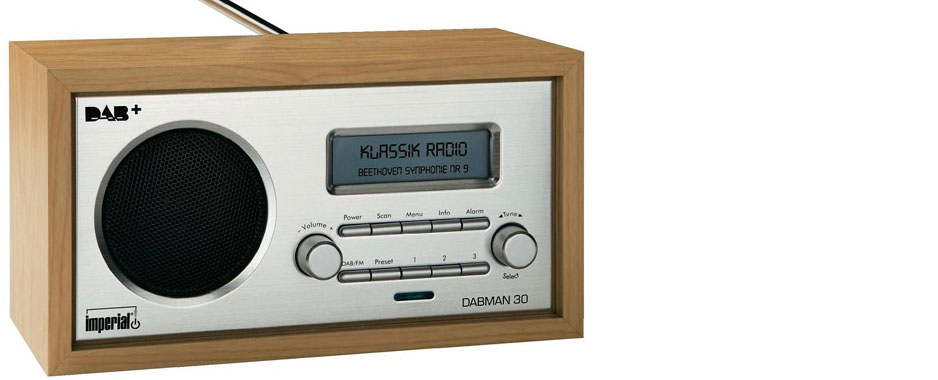
South Africa still hasn’t switched on commercial digital terrestrial television broadcasts, but that isn’t holding back the broadcasting industry from running trials to test digital radio broadcasts based on Digital Audio Broadcasting and Digital Radio Mondiale
There are some specific words that are not particularly popular with the European Commission: “hi-tech”, “anticompetitive” and “bundling”, to name a few. Throw “US firms” into the mix, and the
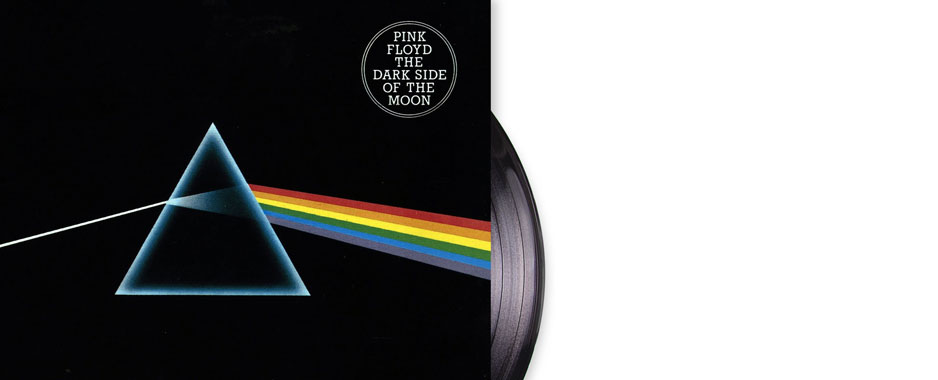
Digital music downloads and online streaming sales have now overtaken sales of CDs and records for the first time, underscoring just how fundamentally the internet has changed the way we consume
In a music buying industry now dominated by iTunes and music streaming services such as Spotify, Napster, Pandora and Jay-Z’s recently released Tidal, the CD and physical music store are reportedly in sharp (and potentially terminal) decline. But a curious development
Just before the Easter long weekend, Eskom ramped up the amount of generation capacity taken offline for planned maintenance by 40%. This was a substantial move (and a very belated positive one). In practical terms, planned maintenance had been hovering around the 4GW