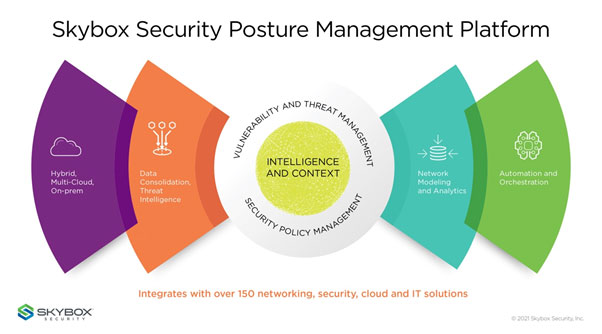
Skybox Security evolved its platform to support customers contending with expediated digital transformation initiatives such as cloud migration and IT/OT convergence. Customers will benefit from:
Skybox Security evolved its platform to support customers contending with expediated digital transformation initiatives such as cloud migration and IT/OT convergence. Customers will benefit from:
Skybox Research Lab key findings – Vulnerability and threat trends report
- Increased agility with more granular insights delivered at a faster speed. To support bespoke organisational and operational workflow requirements, the Skybox platform includes new reporting capabilities with advanced dashboards, sophisticated data visualisation features, and the ability to ingest and process more diverse data sets at higher rates.
- Greater visibility across hybrid networks. Skybox continues to grow its comprehensive list of 150-plus technology partnerships with new connectors that combine rich data from leading SD-WAN and SASE vendors such as Versa Networks and Zscaler. This release also extends support for Check Point, Cisco and Forcepoint.
- Optimised attack simulation. Deeper insights into exposure and risk in near real time allow customers to develop the ideal remediation strategy and reduce mean time to remediation. Customers with highly complex network models will significantly benefit from these performance enhancements.
The industry’s most comprehensive exposure analysis
Enterprises must optimise remediation strategies to focus quickly on the highest exposure risk to address the rise in vulnerabilities, expanding attack surface, sophisticated threat actors and talent shortages. To calculate exposure, Skybox identifies exploitable vulnerabilities and uniquely correlates this data with network configurations and security controls to determine possible exposure.
Exposure analysis is only possible when disparate data repositories are normalised and brought together into a network model, including patch and asset management systems, vulnerability data, threat intelligence feeds, and cloud and network device configurations. The network model provides a dynamic representation of hybrid environments across corporate networks, private cloud, public cloud and OT.
Skybox uniquely enables multi-factor risk prioritisation to conduct the most comprehensive exposure analysis available today through a combination of:
- CVSS scoring: Calculated by importing and merging data from multiple active scanners, Web and application scans, EDR integrations, and Skybox’s own passive detection capabilities.
- Asset importance: Identifies whether assets are mission critical or would expose sensitive data.
- Exploitability: Determines if a vulnerability has been exploited in the wild, with Skybox Research Lab tracking tens of thousands of new vulnerabilities yearly on more than 8 000 products.
- Exposure analysis: Determines which attack vectors can be exploited given the security controls and their configurations.
“I look at data from scanners and say, ‘So what?’ I need to understand what the true risk is that I’m carrying. I need to know what other controls I have in place and whether I should put in time and effort to apply a patch,” said Rebecca Wynn, a well-known chief information security officer. “Failing to ask ‘so what?’ is a critical failure. To make the data useful, I need to know what needs to be patched first and what the order of patches needs to be.”
 Accelerated platform adoption
Accelerated platform adoption
A diverse list of new customers implemented Skybox in 2020, including Fortune 1000 companies, major financial institutions, energy and utility leaders, large retailers, healthcare organisations, numerous government agencies, and local governments. Skybox also saw continued expansion of its Vulnerability and Threat Management Solution, particularly in highly regulated, complex industries, including financial services and critical infrastructure. Nearly 60% of sales came from existing satisfied customers expanding their deployments.
- Platform overview: Skybox Security Posture Management Platform
- Research: Vulnerability and threat trends report
About Skybox Security
Over 500 of the largest and most security-conscious enterprises in the world rely on Skybox for the insights and assurance required to stay ahead of dynamically changing attack surfaces. Our Security Posture Management Platform delivers complete visibility, analytics and automation to quickly map, prioritise and remediate vulnerabilities across your organisation. The vendor-agnostic solution intelligently optimises security policies, actions and change processes across all corporate networks and cloud environments. With Skybox, security teams can now focus on the most strategic business initiatives while ensuring enterprises remain protected. Visit www.skyboxsecurity.com for more information.
Check out all the recent Skybox Security content on hub.techcentral.co.za/skybox.
- This promoted content was paid for by the party concerned