 Leaders at Nasa, who make decisions on multibillion-dollar projects that take years to execute and face many unknowns, have used the “digital twin” concept since the 1970s. For missions that are nearly impossible to reach or repair once launched, simulating conditions in advance became essential.
Leaders at Nasa, who make decisions on multibillion-dollar projects that take years to execute and face many unknowns, have used the “digital twin” concept since the 1970s. For missions that are nearly impossible to reach or repair once launched, simulating conditions in advance became essential.
The technology has gained wider traction in recent years as data infrastructure and AI capabilities have improved. Today its use in cybersecurity is reaching a critical point of adoption.
“Imagine if every critical system had a living, learning digital mirror that could predict attacks before they occur,” said Nithen Naidoo, CEO of Snode. “This technology is hugely valuable in cybersecurity as attack patterns become more complex and difficult to game out.”
Despite sounding like science-fiction, digital twin technology is not a concept of the future but a reality of today. Snode is actively helping clients navigate this technological shift by securely implementing digital twin infrastructure in their environments, ensuring sufficient flexibility to accommodate continuous improvements.
As more global enterprise technology leaders, including Snode’s clients, invest in digital twin technology, the market is set to soar. With a reported value of US$35-billion in 2024, the market is projected to reach a staggering $379-billion by 2034, according to Gartner. This growth reflects rising demand, practical use cases and a need for more responsive systems.
From digital model to digital twin
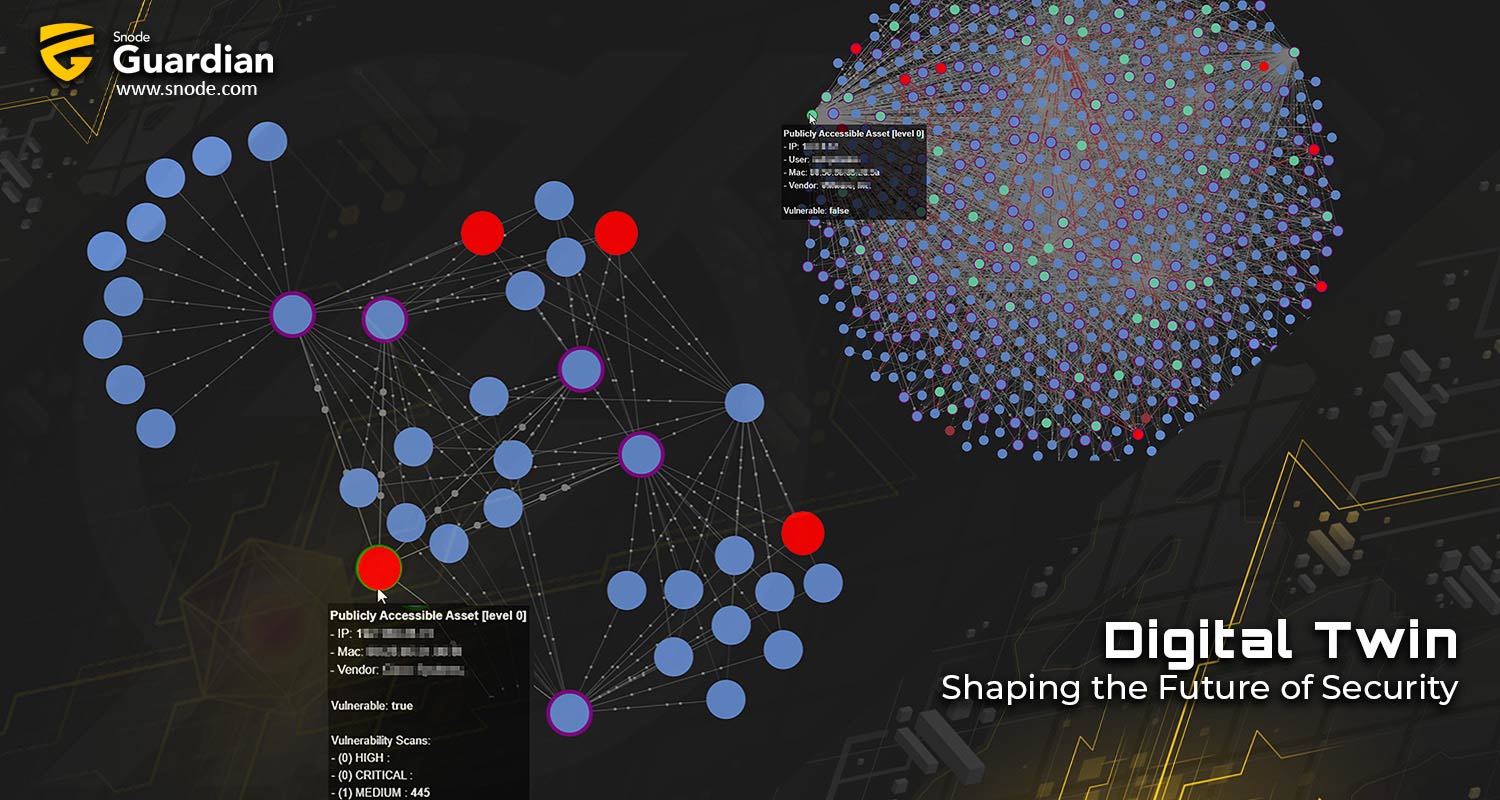
A digital twin is a live, synchronised digital replica of a complex system. It is characterised by active, bidirectional, real-time integration across all data sources.
This differs from “digital shadows”, which only accommodate one-way data flow, or limited, static digital models, often created as “read-only” dashboards or representations.
“Digital twins don’t just observe but can also influence an environment in real-time” said Naidoo. “This represents a step-change in the way in which we can make quality decisions and take efficient action. This is particularly useful in cybersecurity, where the need for continuous situational awareness is growing, and a CISO’s ability to prioritise and respond to threats has never been more valued.
How AI-driven digital twins empower self-defending networks
As AI develops at an increasing speed, pairing this technology with digital twin capability ushers in the era of autonomous resilience for cybersecurity. This convergence unlocks our ability to transition from predictive analysis (the use of live and historical data to forecast potential exploits) to predictive models (which recommend specific, direct actions based on simulated outcomes) and, finally, to autonomous response (which executes real-time containment and mitigation). AI’s role in this process is to analyse the data, identify potential threats, and recommend or implement appropriate responses.

Naidoo said: “Bidirectional communication between the real world and mirror copy (digital twin) not only implies that we can predict, simulate and model future states but that we can automatically respond to threats in real time with highly efficient mitigation strategies or remedial action. This moves cybersecurity from a reactive posture to real proactive autonomous defence. Threats can now be anticipated, understood and neutralised, at machine speed, within the context of the entire system.”
This builds resilience into the fabric of an environment, ensuring that protection scales with the complexity and intensity of threats. It gives CISOs an immediate advantage in steering the safety of their enterprises, assets, people and even physical environments. This makes exploring the technology now a necessity, not a desire.
About Snode Technologies
Founded in 2016, Snode Technologies is a cybersecurity company specialising in AI- and machine learning-powered technology, combined with specialist-led managed services. The company helps organisations detect, prioritise and respond to cyberthreats in real time. Snode partners closely with clients across sectors to elevate their cyber maturity, reduce operational risk and strengthen decision making through actionable intelligence. Headquartered in South Africa, Snode continues to expand its global presence while staying true to its core mission: enabling collective, proactive defence through technology and trust. For more, please reach out to Kira Hartig on [email protected] or call 012 880 0989. Learn more at www.snode.com.
- Read more articles by Snode on TechCentral
- This promoted content was paid for by the party concerned
Don’t miss:
TCS+ | Snode CEO Nithen Naidoo on the cybersecurity opportunity