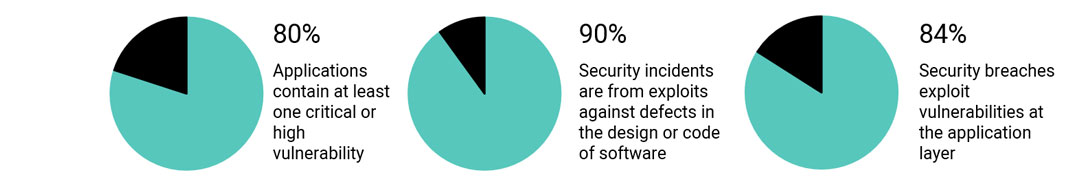
 The majority of security breaches today are due to application vulnerabilities. According to Micro Focus Software Security Research’s 2018 Application Security Risk Report, 80% of applications contain at least one critical or high vulnerability and 90% of security incidents are from exploits against defects in the design or code of software.
The majority of security breaches today are due to application vulnerabilities. According to Micro Focus Software Security Research’s 2018 Application Security Risk Report, 80% of applications contain at least one critical or high vulnerability and 90% of security incidents are from exploits against defects in the design or code of software.
We know that cyberthreats are wreaking havoc on businesses across the globe, but did you know that 84% of security breaches exploit vulnerabilities at the application layer because of the critical vulnerabilities mentioned above?
Unfortunately, while software security is becoming a higher priority, for many businesses it’s still an afterthought — one-quarter of respondents reported that their application security program covers only 1% to 25% percent of their apps. Almost 79% of applications contain at least one critical or high vulnerability.
Here’s what makes these statistics even scarier: in recent years, software has gone from being a support function of business to becoming an innovation centre. Applications and software platforms have become essential competitive differentiators for most businesses in every vertical and size.
With this shift in the role of software, businesses today are dramatically increasing the number of applications they develop and the frequency of releases to the market.
However, while software has become the enabler of innovation, it has also become a source of vulnerability for organisations.
 Not knowing if or when there are security vulnerabilities created in the software development and post-deployment lifecycles of applications has left businesses exposed, and placed security squarely at the forefront of development.
Not knowing if or when there are security vulnerabilities created in the software development and post-deployment lifecycles of applications has left businesses exposed, and placed security squarely at the forefront of development.
Simply put, the realities and frustrations of managing an increasingly fast-paced app development landscape as well as the impossibilities and impracticalities of trying to manage code vulnerabilities in real-time and on their own in an exponential world have left organisations exposed.
This is only amplified by the fact that modern applications are also increasing in complexity due to the need for speed, and as a result, developers’ reliance on code re-use as well as open-source and commercial (COTS) components has increased dramatically.
Why does this leave organisations even more exposed? Because some of the notable security breaches in recent years were due to vulnerabilities in third-party code components.
Security teams today are tasked with finding and managing vulnerabilities as early as the development cycle.
Download the white paper and find out how to secure your applications at the speed of DevOps with Fortify on Demand from Micro Focus in partnership with EOH.
The role of DevSecOps
DevOps is a set of practices that automates the processes between software development and IT teams, in order that they can build, test and release software faster and more reliably. The concept of DevOps is founded on building a culture of collaboration between teams that historically functioned in relative silos.
As businesses dramatically increase the number of applications they release each year, the need for speed and agility has also increased exponentially. DevOps is a critical factor in an organisation’s ability to deliver both.
Increasingly, however, DevOps isn’t just about development and operations teams. If you want to take full advantage of the agility and responsiveness of a DevOps approach, IT security must also play an integrated role in the full lifecycle of your apps.
In the past, the role of security was isolated to a specific team in the final stage of development. That wasn’t as problematic when development cycles lasted months or even years, but those days are over. Effective DevOps ensures rapid and frequent development cycles (sometimes weeks or days), but outdated security practices can undo even the most efficient DevOps initiatives.
 Now, in the collaborative framework of DevOps, security is a shared responsibility integrated from end to end. The term DevSecOps has been coined to emphasise the need to build a security foundation into DevOps initiatives.
Now, in the collaborative framework of DevOps, security is a shared responsibility integrated from end to end. The term DevSecOps has been coined to emphasise the need to build a security foundation into DevOps initiatives.
DevSecOps means thinking about application and infrastructure security from the start. It also means automating some security gates to keep the DevOps workflow from slowing down.
Selecting the right tools to continuously integrate security can help meet your security goals, but effective DevOps security requires more than new tools — it builds on the cultural changes of DevOps to integrate the work of security teams sooner rather than later.
Download the white paper and find out how to secure your applications at the speed of DevOps with Fortify on Demand from Micro Focus in partnership with EOH.
Secure what matters most
According to Harvard Business Review, the long-term answer to cybersecurity lies in dividing which cybersecurity challenges should be the responsibility of individual companies and which should come from platforms and services that take responsibility for foundational security — in other words, security as a service, or SECaaS.
This model allows technology and service providers to make not only necessary, but extraordinary R&D investments to create the best possible security capabilities and practices for all companies. A platform provider spending US$1-billion and hiring from the top of the security talent pool to provide shared capabilities to 100 companies produces far more benefit than those 100 companies spending $100-million each on the same “undifferentiated heavy lifting”.
Combining DevSecOps with the right security provider will ensure protection from loss of revenue and reputational damage.
Micro Focus maintains a leader position in the Magic Quadrant for Application Security Testing for our Fortify offering based on our completeness of vision and ability to execute.
Fortify on Demand lets you trust the security of your software.
Cyberthreats are escalating. Ageing apps and processes (along with new ones) are full of unforeseen risks. Privacy and compliance requirements are mounting. And point solutions don’t offer the scope, vision, or cross-silo analytics needed for these company-wide challenges.
With Fortify on Demand, you can take a holistic, analytics-driven approach to securing what matters most in your business — identities, applications and data.
Our Security, Risk and Governance solutions help you:
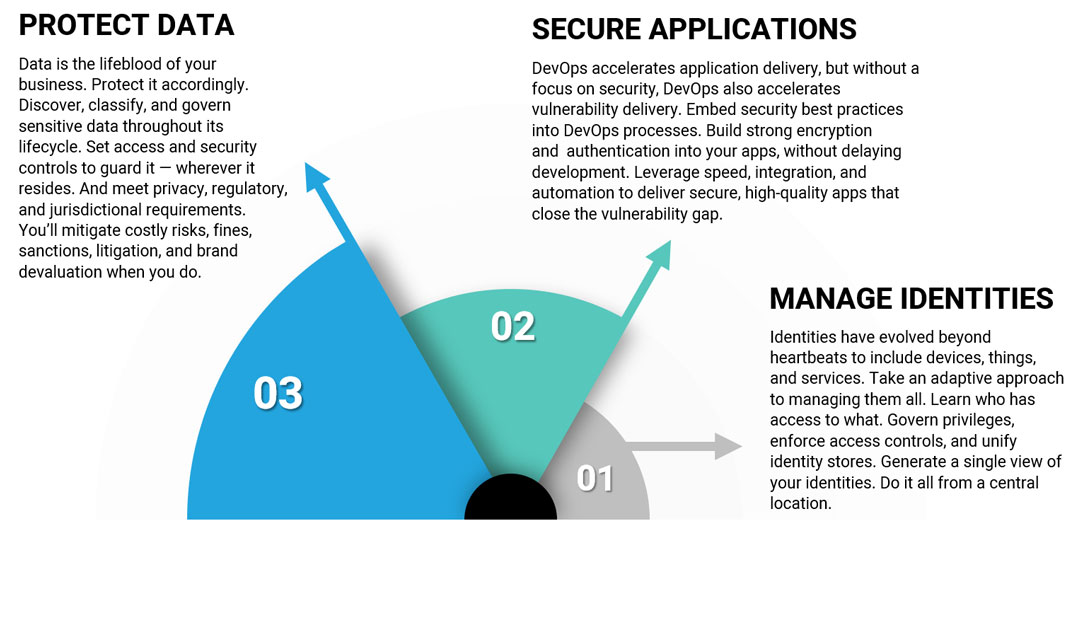
1. Manage identities
Identities have evolved beyond heartbeats to include devices, things and services. Take an adaptive approach to managing them all. Learn who has access to what. Govern privileges, enforce access controls and unify identity stores. Generate a single view of your identities. Do it all from a central location.
2. Secure applications
DevOps accelerates application delivery, but without a focus on security, DevOps also accelerates vulnerability delivery. Embed security best practices into DevOps processes. Build strong encryption and authentication into your apps, without delaying development. Leverage speed, integration and automation to deliver secure, high-quality apps that close the vulnerability gap.
3. Protect data
Data is the lifeblood of your business. Protect it accordingly. Discover, classify and govern sensitive data throughout its lifecycle. Set access and security controls to guard it — wherever it resides. And meet privacy, regulatory and jurisdictional requirements. You’ll mitigate costly risks, fines, sanctions, litigation and brand devaluation when you do.
Fortify offers end-to-end application security solutions with the flexibility of testing on-premises and on-demand to cover the entire software development lifecycle. Complete software security assurance with Fortify on Demand — our application security as a service — integrates static, dynamic and mobile AppSec testing with continuous monitoring for web apps in production.
Download the white paper and find out how to secure your applications at the speed of DevOps with Fortify on Demand from Micro Focus in partnership with EOH.
About Micro Focus
At Micro Focus, we help you run and transform your business. Driven by customer-centric innovation, our software provides the critical tools you need to build, operate, secure and analyse the enterprise. By design, these tools bridge the gap between existing and emerging technologies — which means you can innovate faster, with less risk, in the race to digital transformation.
About Fortify on Demand
Fortify offers end-to-end application security solutions with the flexibility of testing on-premises and on-demand to cover the entire software development lifecycle. Complete software security assurance with Fortify on Demand — our application security as a service — integrates static, dynamic and mobile AppSec testing with continuous monitoring for Web apps in production, delivering security testing, vulnerability management, expertise and support. Fortify on Demand makes it easy to create, supplement and expand a complete Software Security Assurance programme, including SAST, DAST, MAST, IAST, RASP, continuous application monitoring and secure developer training.
- Contact: Allyson Towle, country marketing manager, Micro Focus, +27-11-322-8300, [email protected]
- This promoted content may have been paid for by the party concerned




