 As the coronavirus pandemic has changed the world around us, organisations have had to adapt to a new, remote way of working, and in response, many have shifted to focus on cloud-first strategies.
As the coronavirus pandemic has changed the world around us, organisations have had to adapt to a new, remote way of working, and in response, many have shifted to focus on cloud-first strategies.
To streamline this transition, ESET has launched ESET Protect, to assist businesses in gaining centralised visibility, management and insights across the security of their endpoints. The ESET Protect platform is available either in the cloud to accommodate businesses looking for affordable and easy deployment, or on-premises for increased control.
Save, save, save
As some businesses find their budgets increasingly squeezed in the face of renewed lockdown restrictions, optimising the use of your money is even more necessary. It may be tempting to leave security aside but moving to the cloud can provide the much-needed savings on cost.
ESET Protect Cloud, for example, takes away the typical cost of server provisioning required for on-premises solutions. Instead, imagine getting rid of hardware – physical servers, backup servers, failover clusters – and not worrying about software updates – server software updates, software component updates, console updates – because that’s all handled by ESET.
Continue to imagine that your business doesn’t need a team of IT administrators to set up and maintain your servers, databases, software and other on-premises infrastructure. Applications that are known to have common vulnerabilities, and which require diligent patching, are no longer your problem.
As a simple, cloud-based product, ESET Protect Cloud needs just one IT administrator sitting at the console to quickly deploy an entire suite of advanced security solutions that can protect your business from attack.
Says Carey van Vlaanderen, CEO of ESET South Africa: “ESET Protect Cloud is the result of the shifting business needs we have seen, keeping our fingers on the pulse of the cybersecurity landscape, and improving our solutions. Many businesses have either had to embrace going online or have had to ramp up their online presence over the last year with their teams relying on online meetings to ensure it’s business as usual for their clients. That’s why now more than ever, cybersecurity needs to be a priority, and the ESET Protect Cloud offering really excites us.”
Seamless, convenient, flexible
Aside from financial benefits, ESET Protect offers a wealth of other benefits. With an easy and quick setup process, administrators can log into the console and start protecting machines in a matter of minutes. ESET Protect’s live installers and wide range of deployment methods enable organisations to install endpoint protection seamlessly across all devices in even the largest corporate network.
Adjusting to each customer’s individual needs, the solution is scalable, allowing businesses to enlarge or reduce the coverage according to the size of their workforce, whether this is in-house or remote. Convenient, customisable reports allow IT administrators to communicate effectively and can be adapted to fit the dynamically changing needs of large or small organisations. All this is achieved without the need for specialised IT personnel, extensive training or additional hardware – and ESET specialists are on hand to provide additional support whenever necessary.
Everything you need in the same place
Not all businesses are the same, and ESET is offering a selection of business products that ensure businesses of all sizes are equipped with the right solutions.
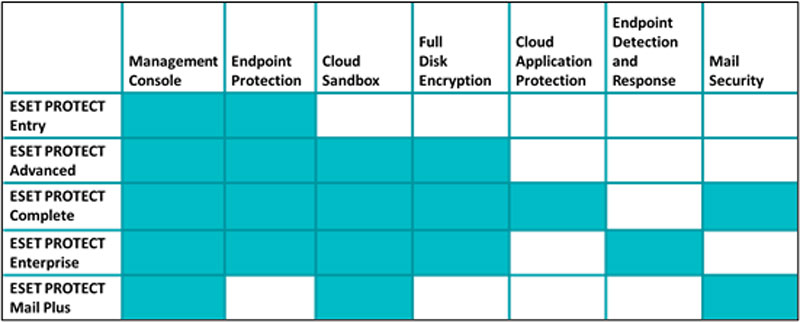
ESET’s business products all include an endpoint management console – either cloud-based or on-premises – along with endpoint protection by default. ESET Protect Mail Plus covers the needs of organisations looking for an advanced mail security solution.
Providing endpoint protection against ransomware and zero-day threats, alongside data protection via full disk encryption, the ESET Protect Advanced product is perfect for small and medium businesses, and managed service providers. The solution is designed to detect suspicious encryption-like activity commonly employed by ransomware and can run machine-learning analyses on high-performance machines in the cloud to more quickly discover novel malicious software aiming to evade detection by endpoint security products.
 For large organisations, the ESET Protect Enterprise option provides comprehensive visibility right down to the techniques commonly used by advanced persistent threat groups. This is because the product offers a highly sophisticated endpoint detection and response solution with rule-based detection, threat hunting and remediation capabilities. By purchasing ESET Protect Enterprise, enterprise customers get all the benefits of ESET Protect Advanced plus endpoint detection and response.
For large organisations, the ESET Protect Enterprise option provides comprehensive visibility right down to the techniques commonly used by advanced persistent threat groups. This is because the product offers a highly sophisticated endpoint detection and response solution with rule-based detection, threat hunting and remediation capabilities. By purchasing ESET Protect Enterprise, enterprise customers get all the benefits of ESET Protect Advanced plus endpoint detection and response.
Says Van Vlaanderen: “We are thrilled to offer solutions for businesses of all sizes that are implementing a ‘cloud-first’ strategy for their IT security. At ESET, we are passionate about safer technology for all, and that means that businesses of all shapes and sizes must be equipped with cutting-edge, tailored solutions to keep their employees and data safe and secure.”
To learn more about ESET Protect Cloud, click here. For other security offerings from ESET, visit our website here.
About ESET
For more than 30 years, ESET has been developing industry-leading IT security software and services to protect businesses, critical infrastructure and consumers worldwide from increasingly sophisticated digital threats. From endpoint and mobile security to endpoint detection and response, as well as encryption and multifactor authentication, ESET’s high-performing, easy-to-use solutions unobtrusively protect and monitor 24/7, updating defences in real time to keep users safe and businesses running without interruption. Evolving threats require an evolving IT security company that enables the safe use of technology. This is backed by ESET’s R&D centres worldwide, working in support of our shared future. For more information, visit www.eset.com or follow us on LinkedIn, Facebook and Twitter.
- This promoted content was paid for by the party concerned




