 In light of the continually shifting cybersecurity landscape, businesses are increasingly being confronted with formidable challenges in securing their digital assets. The rapid advancements in technologies such as artificial intelligence and the internet of things have ushered in a new wave of cyberthreats. In this article, Avert ITD delves into the latest developments in the field of cybersecurity.
In light of the continually shifting cybersecurity landscape, businesses are increasingly being confronted with formidable challenges in securing their digital assets. The rapid advancements in technologies such as artificial intelligence and the internet of things have ushered in a new wave of cyberthreats. In this article, Avert ITD delves into the latest developments in the field of cybersecurity.
 Ransomware
Ransomware
As AI continues to advance, so, too, does the sophistication of ransomware, posing greater challenges to cybersecurity. These evolving strains are now capable of adapting to diverse security environments, making detection and neutralisation more difficult.
Moreover, the rise of “double extortion” tactics, where attackers not only encrypt data but also threaten to leak it, has significantly increased the risks for businesses across various sectors. This threat is particularly acute for healthcare institutions, which are heavily reliant on specialised software systems.
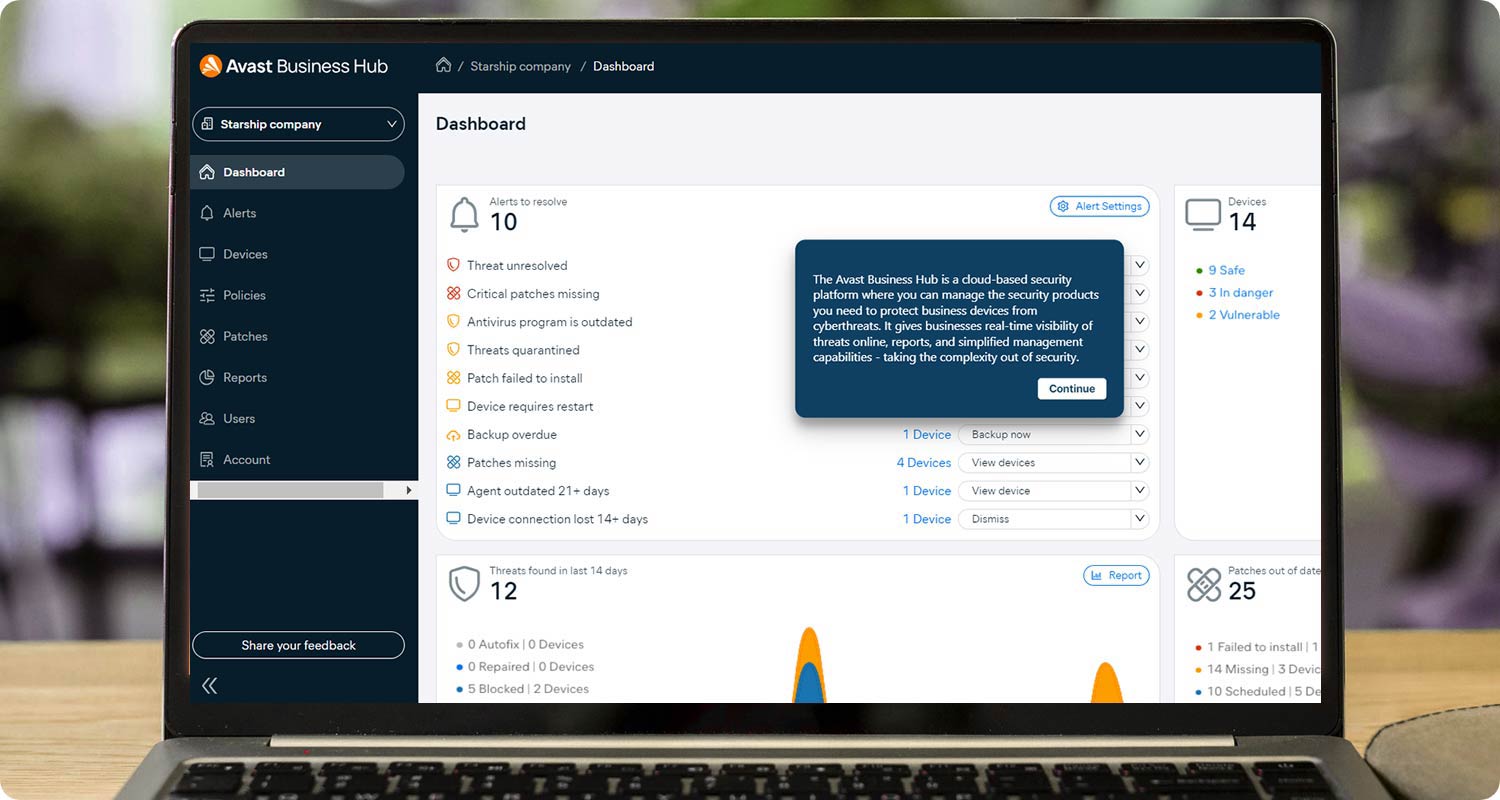
In response to these escalating threats, robust security measures and proactive strategies are imperative. Avast and AVG, renowned for their comprehensive cybersecurity solutions, play a crucial role in defending against ransomware attacks. Their advanced threat detection technologies, combined with real-time monitoring and behavioural analysis, can identify and thwart ransomware attempts before they inflict damage.
Furthermore, Avast and AVG’s proactive ransomware protection features, such as behaviour-based blocking and automatic sandboxing of suspicious files, provide an additional layer of defence. These tools not only safeguard critical data but also ensure business continuity by preventing disruptions caused by ransomware incidents.
In conclusion, in the face of increasingly sophisticated ransomware and the growing prevalence of double extortion tactics, leveraging Avast and AVG’s advanced security capabilities is essential. By implementing these solutions, businesses can significantly enhance their resilience against evolving cyberthreats while maintaining vigilance against emerging vulnerabilities.
 Backup and cloud security
Backup and cloud security
As more businesses transition to online and cloud backup solutions, the nature of threats against these security measures has evolved accordingly. Cloud backups are increasingly vital for securing cloud-native environments and data, yet the risk of data breaches during transit or storage in the cloud has become a significant concern for IT departments and service providers alike.
To mitigate these risks, implementing encrypted backups is crucial. Solutions like Barracuda’s Cloud-to-Cloud Backup offer robust encryption protocols, ensuring that data is stored securely and remains accessible even in the event of a breach.
Additionally, tools like Macrium backup provide another layer of protection by enabling reliable data backup and recovery for a variety of platforms, including Windows environments. This comprehensive approach helps businesses safeguard their critical data against potential security threats, bolstering their resilience in the face of evolving cybersecurity challenges.
 Remote work
Remote work
With the shift to remote work becoming increasingly prevalent, there has been a corresponding rise in exploiting less secure network connections to gain access to company infrastructure. Therefore, it is imperative for organisations to prioritise the implementation of robust security measures such as multifactor authentication and secure VPNs. These measures enhance security for remote workers connecting to organisational systems and networks. Additionally, ensuring that remote connections are encrypted with tools like AnyDesk significantly improves security and reduces the risk of exploitation.
The benefits of using AnyDesk extend to its efficiency in facilitating secure remote connections. AnyDesk provides encrypted connections that safeguard data integrity and confidentiality during remote access sessions. This not only enhances security but also promotes seamless collaboration and productivity among remote teams. By utilising AnyDesk, organisations can ensure their remote operations remain secure and resilient against cyberthreats, thereby safeguarding critical digital infrastructure and maintaining business continuity.
About Avert ITD
With our focused approach to support and technical knowledge, Avert ITD is a dedicated software and security appliance distributor throughout Africa. To prevent delays in everyday performance, we offer technical support and training to company members to ensure a seamless workflow and boost return on investment. For more information, visit avertitd.com or connect on LinkedIn. Phone +27(0)100074430 (Johannesburg) or +27(0)210072655 (Cape Town) or e-mail [email protected].
- This promoted content was paid for by the party concerned
- Read more articles by Avert ITD on TechCentral




