IBM predicts advancements in quantum computing will likely lead to the first quantum cyberattack – or Q-Day – by as soon as next decade.
“The first quantum attacks will be by highly resourced entities, perhaps even nations states, and they will target high-value assets,” said Antti Ropponen, executive partner and global data and application security services leader at IBM Cybersecurity Services.
One of the key risks posed by quantum computers, which are exponentially more powerful than traditional computers, is that bad actors will use their computing power to break traditional cryptographic tools upon which most of the world’s security systems are based. And they’ll be able to do it with ease.
However, according to Ropponen, organisations can achieve quantum safety without necessarily having access to quantum computing tools themselves.
“If we look at quantum-safe technology overall, it is about systems that are resilient to the risk from quantum computing being used in malicious ways. There are three broad categories when it comes to quantum safety: post-quantum cryptography, quantum key distribution and quantum random number generators,” said Ropponen. “We often hear that to be quantum safe, you need to use a quantum computer. But the answer to that is no.”
Quantum computers get their power from their ability to use quantum super-positioning to encode more data than a traditional computer can. Whereas a traditional computer can use one of its bits for either one of two representations, a zero or a one, a quantum bit – or qubit – can represent a zero, one and any combination of the two in the same space.
Breaking bad
Quantum computers can run multiple calculations in parallel, reducing the time it takes to get to a solution. Modern 2 048-bit encryption technology relies on the fact that it would take today’s most advanced supercomputers about a billion years to break it. A quantum computer could do it in 100 seconds.
According to Ropponen, organisations are in danger from bad actors whose aim is to steal encrypted data, store it for a few years and then use quantum computing to decrypt it only to use it nefariously at an opportune moment.
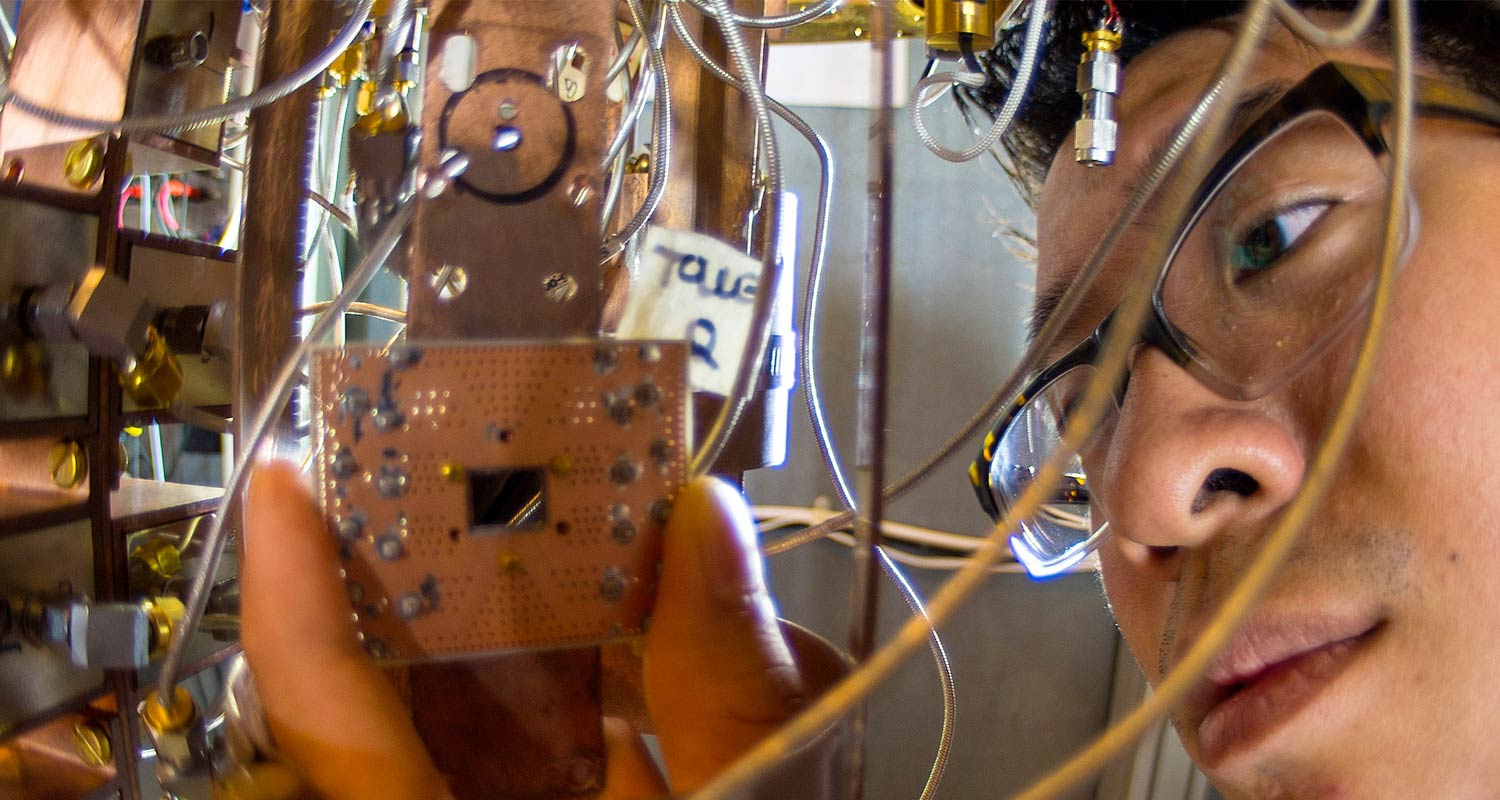
IBM Research is developing cryptographic solutions using quantum computers that other such computers will not be able to break.
Read: Quantum computing will spark ‘cybersecurity Armageddon’
Cryptographic keys designed in this way can be used by traditional computers but transporting them safely from where they are generated to the machine that will use them is another key area of research.
IBM sells cloud-based quantum computing capacity to governments, educational institutions and researchers, and is already seeing uptake from South African organisations. Molecular sequencing, weather prediction and advanced financial modelling are just some of the ways quantum computing is being used in real-world applications.

IBM said it has a vigorous vetting process to assess the integrity of organisations applying to access its quantum computing network. This is in part in an effort to lock out bad actors.
Shor’s algorithm, developed by mathematician Peter Shor in 1994, is a quantum algorithm designed to factorise large composite numbers, the key to breaking traditional encryption. According to Ropponen, IBM has security protocols on its quantum computing network that prevent the use of Shor’s algorithm, too.
The pressure on organisation to transition their IT practices into the quantum era is not only because of the threat of bad actors. IBM has observed that regulators in Singapore, the US and Germany are already adding quantum-safe encryption standards into their data safety standards, especially in the financial sector. The company said card payment industry standards are going to have to change to keep up with advancements in quantum computing. – © 2024 NewsCentral Media




